10 Cybersecurity Best Practices That Prevent Breaches

Sixty percent of breaches still involve human actions (Verizon DBIR, 2025). Organisations know they should train employees, enforce MFA, and patch systems. Most have policies that say exactly that.
The problem is not knowledge. The disconnect is between knowing what to do and implementing it consistently, it always comes to down to the basics but doing them really well is where most fail.
This guide covers 10 cybersecurity best practices backed by current breach data, with practical guidance on making each one operational.
Get practical security insights delivered weekly. Subscribe to CyberDesserts for threat intelligence and implementation guidance.
Table of Contents
- Implement Zero Trust Architecture
- Enforce Multi-Factor Authentication
- Patch Vulnerabilities Faster
- Transform Security Awareness Training
- Build Detection and Response Capability
- Secure Your Supply Chain
- Address AI Security Risks
- Build A Security Culture
- Align with a Security Framework
- Secure Remote Workers
1. Implement Zero Trust Architecture
Traditional perimeter security assumes everything inside the network is trusted. Attackers exploit this assumption. Once inside, they move laterally with minimal resistance, often using legitimate credentials that blend into normal traffic.
Zero trust inverts this model: never trust, always verify. Every access request is authenticated and authorised regardless of where it originates. The 2025 Verizon DBIR found that credential abuse initiated 22% of breaches. Lateral movement after initial access often causes more damage than the initial compromise itself.
Least privilege Users and systems should receive only the access required for their specific function. When an account is compromised, the blast radius is contained.
Zero trust also forces honest conversations about legacy infrastructure. Systems that cannot support modern authentication become visible risks rather than hidden assumptions.
Start with identity: strong authentication, conditional access policies, and privileged access management. Extend to network segmentation. Add continuous monitoring for anomalous access patterns.
2. Enforce Multi-Factor Authentication
MFA remains the single most effective control against credential-based attacks. The 2025 Verizon DBIR found that 88% of basic web application attacks involved stolen credentials.
The challenge is coverage, not technology. Shadow IT bypasses corporate identity. Exceptions accumulate until the control has more holes than protection.
Treat MFA as non-negotiable for all systems that touch sensitive data. Track coverage as a board-level metric. When a system cannot support MFA, create a migration plan, not an indefinite exception.
3. Patch Vulnerabilities Faster
The 2025 Verizon DBIR shows vulnerability exploitation increased 34% year over year. Only 54% of edge device vulnerabilities get patched, with a median fix time of 32 days.
Thirty-two days is an eternity when attackers are scanning continuously.
The shift toward continuous threat exposure management reflects this reality: organisations need to prioritise remediation based on actual risk, not just CVSS scores. The difference between effective and ineffective programmes comes down to ownership and clear SLAs.
Integrate vulnerability scanning with threat intelligence. A medium-severity vulnerability being actively exploited matters more than a critical one with no public exploit. See the NIST-Aligned CTEM guide for implementation details.
4. Transform Security Awareness Training
Phishing simulation click rates plateau around 1.5% regardless of how much training organisations deliver (Verizon DBIR, 2025). But user reporting of suspicious emails increased fourfold after effective training programmes.
The goal is not eliminating all clicks. The goal is building a culture where employees report suspicious activity quickly.
Only 32% of employees engage with cybersecurity awareness training (CybSafe, 2025). Among those who do, fewer than half change their behaviour. The knowing-doing gap is real.
Replace annual compliance training with adaptive micro-learning. International Game Technology transformed from 30% phishing failure rates to 4-6% using this approach. Measure reporting rates, not just click rates.
5. Build Detection and Response Capability
Prevention controls will fail. The organisations that limit breach impact detect intrusions quickly and respond effectively.
The average breach lifecycle dropped to 241 days in 2025, the lowest in nine years (IBM). Organisations using AI-powered security tools cut that lifecycle by 80 days and saved nearly $1.9 million on average.
The 2025 IBM report found that 76% of organisations took more than 100 days to fully recover from a breach. Regular tabletop exercises reveal gaps before real incidents expose them.
Focus monitoring on what matters: authentication events, privileged account usage, network traffic anomalies, endpoint behaviour. Our ELK Stack Security Monitoring Tutorial provides a practical starting point.
6. Secure Your Supply Chain
Third-party involvement in breaches doubled year over year, now accounting for 30% of all incidents (Verizon DBIR, 2025). In 2021, Gartner predicted 45% of organisations would experience supply chain attacks by 2025. Reality exceeded forecast: 75% have already experienced one (BlackBerry, 2024).
Supply chain breaches cost 17 times more to remediate than direct attacks. The average is $4.91 million globally.
Sonatype documented 512,847 malicious packages in one year, a 156% year-over-year increase. See the Threat Landscape report where we discuss an escalation of supply chained based attacks in 2025.
Map your supply chain first. Which vendors have access to sensitive data? Implement continuous monitoring rather than annual questionnaires. For development teams, security scanning must be part of the CI/CD pipeline. See the npm Vulnerability Scanner guide for JavaScript environments.
7. Address AI Security Risks
IBM's 2025 Cost of a Data Breach Report found that 63% of breached organisations lacked AI governance policies. Nearly all that suffered AI-related breaches (97%) had no proper access controls.
AI security is now the top skills gap at 41% of organisations, overtaking cloud security for the first time (ISC2, 2025).
The 2025 threat landscape shows AI creating new attack surfaces while also enabling defenders. Attackers use AI to scale phishing and automate reconnaissance. Defenders use it to accelerate detection.
Establish AI governance policies before deployment. Implement access controls for AI systems. Understand both AI security threats and AI-powered defences.
8. Build A Security Culture
Technology alone cannot solve security challenges. Security culture represents the collective behaviours that emerge when employees believe no one is watching.
Employees in organisations with poor security culture are 52 times more likely to share credentials during phishing attacks (KnowBe4, 2025). Teams experiencing emotional disengagement have nearly 3x as many internal security incidents. Teams operating in fear of retribution experience nearly 4x as many (Forrester, 2024).
The foundation is psychological safety. A culture where admitting "I clicked a suspicious link" triggers disciplinary action is a culture where incidents go unreported.
Measure behaviour, not compliance. Track phishing reporting rate (target >55%), mean time to report suspicious activity (<5 minutes), and validated user-reported incidents.
9. Align with a Security Framework
Picking one framework and implementing it thoroughly beats addressing multiple frameworks superficially.
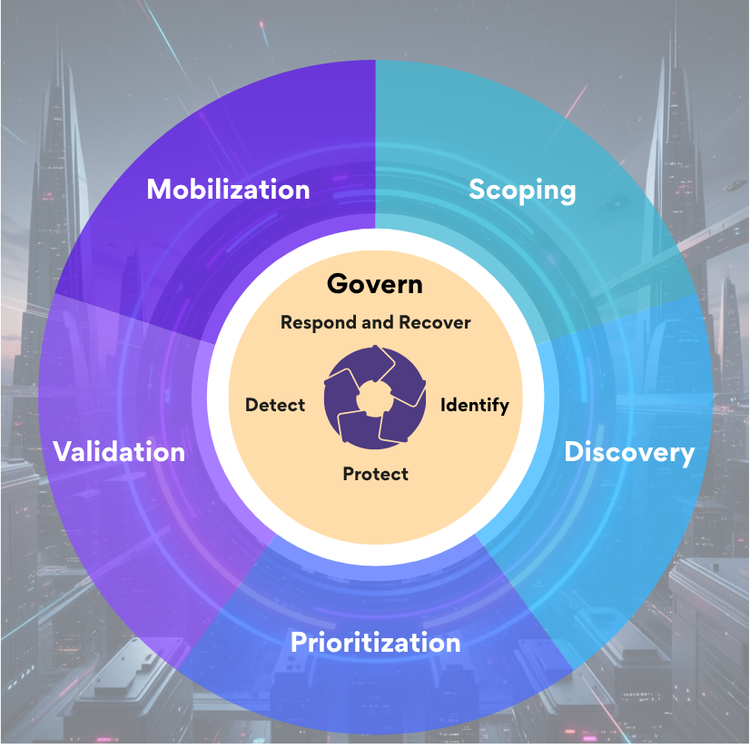
NIST CSF 2.0 provides comprehensive coverage across six core functions: govern, identify, protect, detect, respond, and recover. For enterprises subject to multiple regulatory requirements, mapping controls once to NIST CSF simplifies compliance.
CIS Controls offer a more prescriptive alternative. Implementation Group 1 covers essential cyber hygiene that every organisation should achieve first.
Choose based on your context. NIST CSF for governance and compliance mapping. CIS Controls for prescriptive implementation steps. For practitioners building expertise, the Cybersecurity Skills Roadmap maps the path.
10. Secure Remote Workers
Distributed workforces expand the attack surface. Employees access corporate resources from home networks, personal devices, and public locations.
VPN or zero-trust network access should be mandatory. Split tunnelling creates risk.
Endpoint security must extend beyond the perimeter. Cloud-managed EDR provides visibility regardless of location.
MFA for all remote access is baseline. Conditional access policies add additional assurance.
Training should address remote-specific risks: phishing that impersonates IT support, vishing that exploits inability to verify callers.
Why These Best Practices Fail
The ISC2 2024 Cybersecurity Workforce Study found a global skills gap of 4.8 million professionals. This is not a headcount problem. Entry-level positions have a 10% worker surplus (Lightcast, 2024). The gap is in specific capabilities: AI security (41%), cloud security (36%), and risk assessment (29%).
Stretched teams default to reactive firefighting. Annual training ignores the Ebbinghaus Forgetting Curve: individuals forget up to 80% of newly learned information within a month without reinforcement.
The organisations that succeed prioritise ruthlessly. Start with zero trust principles: assume breach, enforce least privilege, limit lateral movement. Layer detection and response because prevention will eventually fail. Treat security culture as a behavioural challenge, not a knowledge problem.

Accelerate Your Learning
Building security expertise takes time. The CyberDesserts Learning Assistant can help you explore specific topics, from threat actor techniques to framework implementation guidance.
Summary
These 10 cybersecurity best practices appear in every framework because the data shows they work.
Start with where you are. Pick the gaps that represent your highest risk. Close them before moving to the next priority, diligence in these areas will make all the difference.
Get weekly security insights. Subscribe to CyberDesserts for practical threat intelligence and implementation guidance.
Last updated: February 2026
References and Sources
- IBM Security. (2025). Cost of a Data Breach Report 2025. 241-day breach lifecycle; 97% of AI breaches lacked access controls.
- Verizon. (2025). 2025 Data Breach Investigations Report. 60% human element; 22% credential abuse; 30% third-party; vulnerability exploitation up 34%.
- ISC2. (2024). Cybersecurity Workforce Study. Global skills gap 4.8 million; AI skills (41%) top demand.
- Lightcast. (2024). Quarterly Cybersecurity Talent Report. Entry-level 10% worker surplus.
- CybSafe. (2025). Oh, Behave! Report. Only 32% engage with training.
- KnowBe4. (2025). Security Culture Report. Poor cultures 52x more likely to share credentials.
- Forrester Research. (2024). Security Culture Impact Study. Disengaged teams 3x more incidents.
- BlackBerry. (2024). Supply Chain Security Survey. 75% experienced supply chain attacks.
- FBI. (2024). Internet Crime Report. BEC $2.77 billion in losses.
- NIST. (2024). Cybersecurity Framework 2.0.


Member discussion