Inside the Scanners Hunting Exposed AI Infrastructure: 72 Hours of Findings
460 source IPs, 11,643 requests, 72 hours. The AI-aware operators in the data enumerated; the exploitation observed targeted credentials, not AI capabilities.
How the UK Government Slashed Cyber Fix Times by 84%
Published March 2026
The UK government has slashed cyber vulnerability fix times by 84%. Through a new nationwide scanning service,
10 Cybersecurity Best Practices That Prevent Breaches
Sixty percent of breaches still involve human actions (Verizon DBIR, 2025). Organisations know they should train employees, enforce MFA, and
What is CTEM? Why Vulnerability Management Alone No Longer Covers the Attack Surface
Most breaches do not start with a vulnerability. CTEM helps answer the question patching alone cannot: what can an attacker still reach in your environment right now?
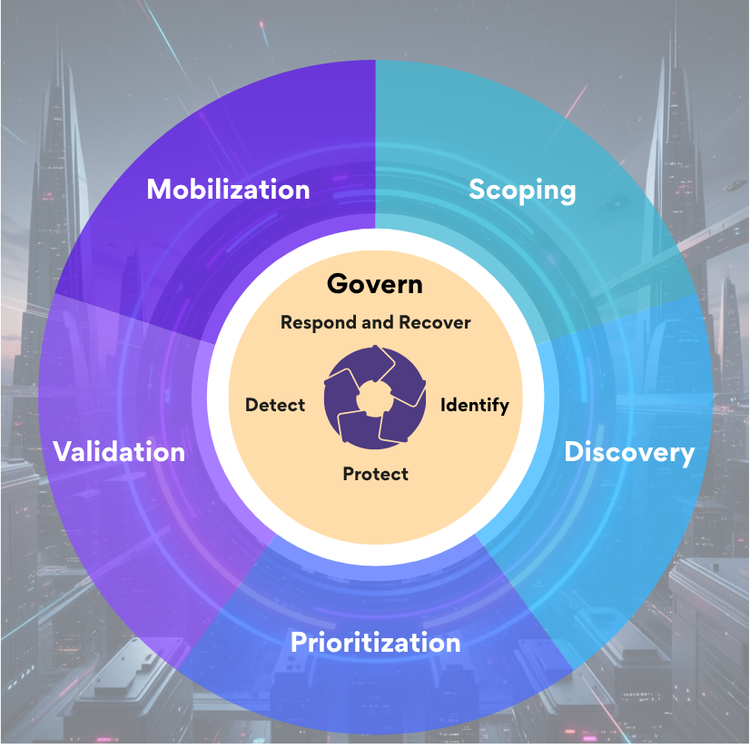
Why NIST Aligned CTEM Is the Framework Integration Security Teams Need
TL;DR - Discover how NIST aligned CTEM transforms framework compliance into operational security. Bridge governance maturity and real threat detection through continuous validation of NIST CSF 2.0 controls.