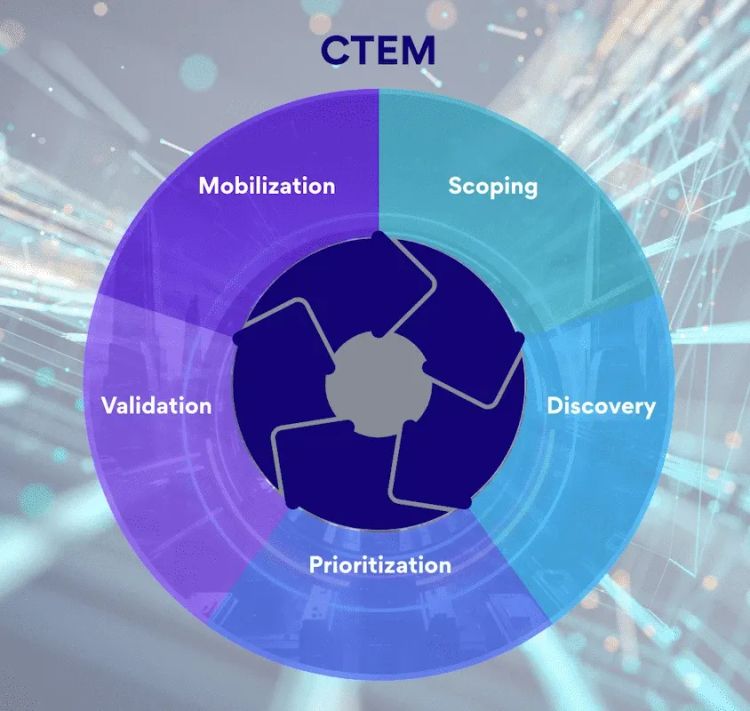
What is CTEM? Complete Guide to Continuous Threat Exposure Management
Gartner predicts that by 2026, organisations prioritising security investments based on a CTEM program will suffer two-thirds fewer breaches. Meanwhile,
npm Security Risks: Most Vulnerable Packages in 2026
Updated March 2026
In 2025, attackers published 454,648 malicious npm packages. That’s nearly half a million in a
Cybersecurity Career Path: Complete Guide for 2026
59% of organisations now report critical or significant cybersecurity skills gaps, up from 44% last year (ISC2, 2025). The narrative
AI Security Threats: Complete Guide to Attack Vectors
Last Updated: January 2026
AI-driven attacks now account for 16% of all breaches (IBM, 2025). Shadow AI adds $670,000
Cybersecurity Learning Roadmap 2026: Beginner to Job-Ready
Updated April 2026
This cybersecurity roadmap takes you from beginner to job-ready in four phases: foundations, core skills, specialisation, and
CVE-2025-55182: React2Shell Detection and Fix Guide
UPDATE (Jan 1, 2026): RondoDox botnet now weaponizing React2Shell. Shadowserver reports 90,300 instances still vulnerable. Multiple nation-state actors actively
What is Cybersecurity Culture? A Practical Guide
Human error accounts for 95% of cybersecurity breaches (IBM Security, 2024). But here is what that statistic misses: employees in
ELK Log Collection Methods: The Complete Guide for Security Teams
A guide to the different types of log collection you can achieve with ELK stack for cybersecurity teams.
What is ELK in Cybersecurity? A Security Professional's Guide
ELK Stack is used by security teams for centralised log management, real-time threat detection, incident response, and compliance logging. This guide covers what it is, whether it qualifies as a SIEM, and when it makes sense to deploy it.
Why npm audit fix Isn't Working
You ran npm audit fix, and nothing changed. The same warnings stare back at you. If this sounds familiar, you&