Cybersecurity Learning Roadmap 2026: Beginner to Job-Ready

Updated April 2026
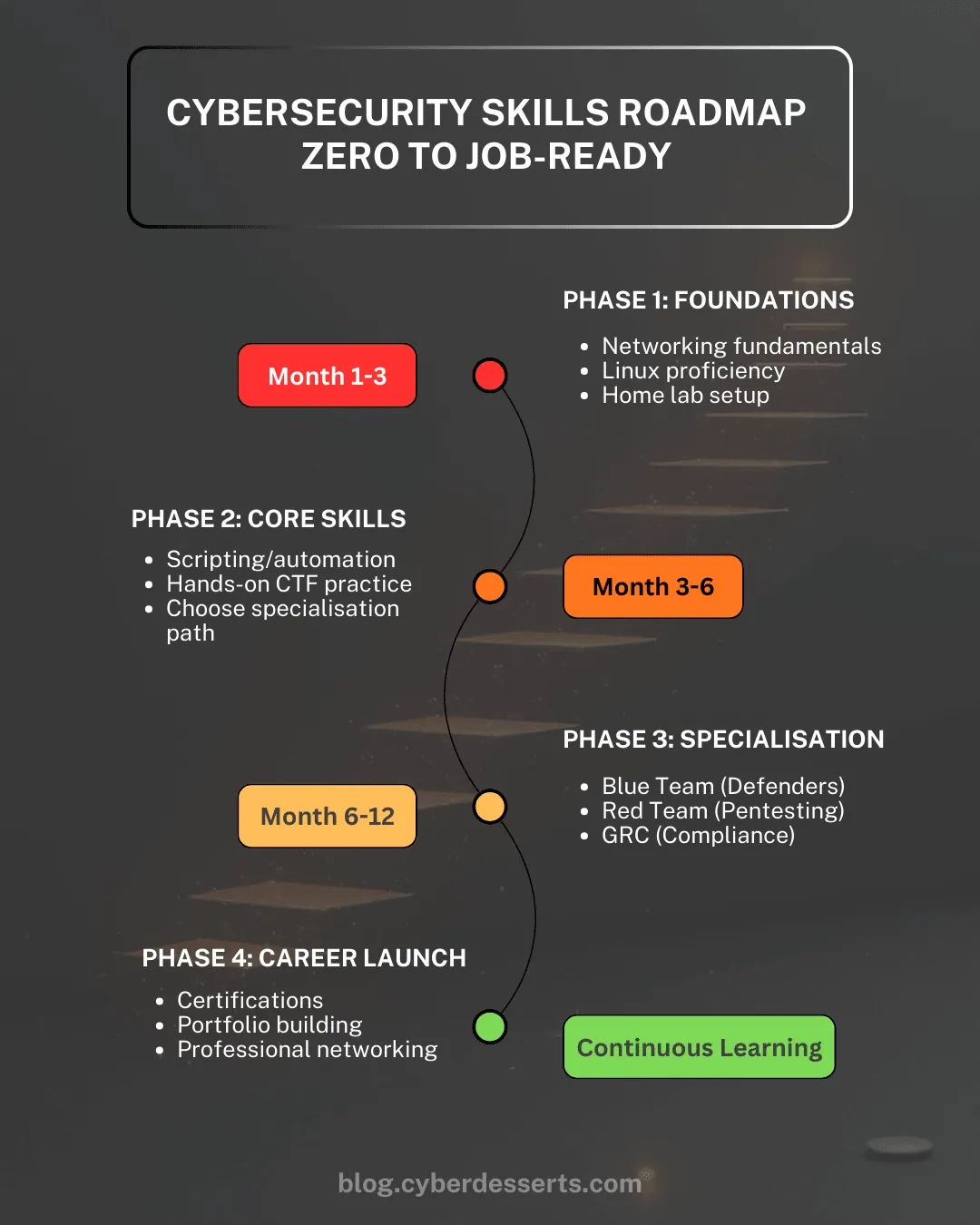
This cybersecurity roadmap takes you from beginner to job-ready in four phases: foundations, core skills, specialisation, and career launch. It is built for people starting from zero who want a practical path into roles like SOC analyst, penetration tester, cloud security, GRC, or DevSecOps, without wasting time on outdated or theory-heavy learning paths.
The focus is on building real, hands-on skills that translate into job-ready capability, not just passing certifications.
• What to learn first
• When to choose a path
• How long it takes
• Which labs, certs, and projects matter
• Where to get the full 58-page guide
What Changed in 2026
• AI security is now a core skill gap
• Blue Team Level 1 has gained more employer recognition
• Cloud and application security remain high-demand
• CREST matters more for UK government-linked work
Most roadmaps tell you what to learn. This one is focused on getting you hired.
59% of cybersecurity teams report critical or significant skills gaps (ISC2, 2025). 88% have experienced at least one significant security consequence because of those gaps. The problem is not a shortage of applicants. It is a shortage of people who can do the work.
56% of hiring managers say it takes 4–9 months to train entry-level hires to handle tasks independently (ISC2 Hiring Trends Report, 2025). They want evidence you can learn, build, troubleshoot, and document your work.
The roadmap breaks the journey into four phases, each building on the previous one. It is also a discovery process that helps you figure out which track fits you best.
Use the table below to choose the track that best matches your interests and starting point.
← Scroll to see full table
| Target Role | Starting Point | Key Phase 3 Skills | First Cert |
|---|---|---|---|
| SOC Analyst | Linux + networking fundamentals | SIEM, threat detection, MITRE ATT&CK | CompTIA Security+ / BTL1 |
| Penetration Tester | Linux + networking + scripting | Web app security, Metasploit, reporting | eJPT → OSCP |
| Cloud Security | Networking + cloud fundamentals | AWS/Azure security, IAM, misconfig detection | AWS Security Specialty / AZ-500 |
| GRC / Compliance | Framework familiarity, risk concepts | NIST CSF, ISO 27001, audit prep | CISA or ISO 27001 Lead Implementer |
| DevSecOps | Scripting + CI/CD basics | Pipeline security, SAST/DAST, SBOM | Security+ + cloud cert |
- Which Cybersecurity Career Path is Right for You?
- Using AI to Learn Cybersecurity Faster
- Phase 1: Essential Skills for Beginners
- Phase 2: Building Core Security Skills
- Phase 3: Specialisation and Advanced Skills
- Phase 4: Getting Your First Cybersecurity Job
- Frequently Asked Questions
- Your 12-Month Action Plan
Which Cybersecurity Career Path is Right for You?
Cybersecurity is not one career path. It is a set of distinct tracks, SOC analyst, penetration tester, cloud security, GRC, each with different skills, tools, and expectations.
One of the biggest mistakes beginners make is jumping into random tutorials without understanding where they are going. The fastest way to progress is to pick a direction early and build towards it deliberately.
This article gives you the structure. The full 58-page guide breaks down each path in detail, including the exact skills, labs, projects, and strategies needed to become job-ready.
Cybersecurity Career Guide Detailed role tracks, lab ideas, AI prompts, portfolio advice, interview prep, and job-readiness guidance.
Using AI to Learn Cybersecurity Faster
AI tools have fundamentally changed how people learn technical skills. Used well, they compress months of struggle into weeks. Used poorly, they create a false sense of competence that collapses in interviews or on the job.
The practitioners who advance fastest treat AI as a sparring partner, not an answer machine. As you move through this roadmap, use AI deliberately at each stage to accelerate your learning. The guidance below shows how to get the most value out of AI.
What AI Does Well
Explaining concepts at your level. Struggling with subnetting? Ask AI to explain it three different ways, or use an analogy that connects to something you understand. Unlike static tutorials, AI adapts to your questions.
Diagnosing errors. Paste an error message with your code or command. AI excels at pattern-matching common problems and explaining what went wrong. This alone saves hours of frustrated searching.
Generating practice scenarios. Ask AI to create CTF-style challenges, quiz you on concepts, or generate realistic log samples for analysis. You can create unlimited practice material tailored to your level.
Translating between formats. Convert detection rules between SIEM platforms. Translate documentation from one tool to another. Reformat data for analysis.
What AI Does Poorly
Current information. AI training has cutoff dates. For recent CVEs, current tool versions, or emerging threats, verify against primary sources.
Replacing hands-on practice. Reading AI explanations of packet analysis is not the same as capturing and analysing packets yourself. Muscle memory comes from doing.
Guaranteeing accuracy. AI confidently produces plausible-sounding nonsense. It invents tool flags that don't exist, cites studies never published, and explains vulnerabilities incorrectly. This is routine, not occasional.
The Critical Thinking Rule
Question everything AI tells you. Verify commands before running them. Test explanations against documentation. If AI suggests a tool or technique, confirm it exists and works as described.
This is not a weakness. It is the skill you are developing. Security professionals must verify information, question assumptions, and validate claims. Practising this with AI output builds the exact mindset employers want.
When AI gives you an answer, ask yourself:
- Does this make sense given what I already know?
- Can I verify this against official documentation?
- What happens if I test this in my lab?
Prompting for Better Results
Vague questions get vague answers. Include your skill level, what you're trying to accomplish, what you've tried, and your specific environment.
Weak: "How do I use Nmap?"
Strong: "I'm scanning a lab network with three VMs. I want to identify all open ports and service versions on 192.168.1.0/24. What Nmap command should I use, and what does each flag do?"
The Responsibility Factor
AI can generate exploit code and attack scripts. Just because you can get this output doesn't mean you should use it carelessly.
In your lab: Experiment freely. Generate attack scenarios, test detection rules, explore techniques.
Against real targets: The same legal and ethical rules apply whether you wrote the code or AI generated it.
In your learning: Generating an answer is not understanding it. If AI writes a script for you, can you explain every line? Modify it? Debug it when it breaks? If not, you haven't learned.
Use AI to learn faster, debug quicker, and explore more widely, while building genuine understanding that holds up when the AI isn't available. Understanding AI capabilities also helps you recognise the threats surrounding AI security in your future self.
Check out this page if you want to see the latest on career trends, which skills and roles matter right now.
Phase 1: Essential Skills for Cybersecurity Beginners (Month 1-3)
The first three months establish the technical base everything else builds on. These skills apply regardless of specialisation. Let me stress you don't need to become an expert at this stage just start to get familiar and comfortable with foundational knowledge, expertise will come later.
Before diving into technical skills, it is important to understand that cybersecurity frameworks, risk, and compliance are not just for GRC roles. Every role in cybersecurity operates within these structures. Whether you are analysing alerts, testing systems, or building secure infrastructure, you are working against defined controls, policies, and risk models. This awareness should develop alongside your technical skills and continue throughout your career.
Networking Fundamentals
You cannot defend or attack systems if you don't understand how they communicate.
Core concepts:
- TCP/IP protocol stack and how data moves across networks
- OSI model and where security controls operate at each layer
- DNS, DHCP, HTTP/HTTPS and common service protocols
- Subnetting, routing, and network architecture basics
Tools: Packet analysis with Wireshark. Network discovery with Nmap.
95% of security professionals use Nmap for network discovery (SANS Survey). The Nmap Scripting Engine guide covers automated vulnerability detection once you have the basics.
Linux Proficiency
96% of the world's top web servers run on Linux (W3Techs). You will use Linux daily in almost any security role.
Skills to develop:
- Command line navigation and file system operations
- User permissions, ownership, and access control
- Process management and system monitoring
- Log analysis and text processing (grep, awk, sed)
- Package management and system configuration
- Basic Bash scripting for automation
Start with Linux Basics for Hackers and follow the Linux for Cybersecurity learning path.
Setting Up a Cybersecurity Home Lab
A personal practice environment lets you learn without legal risk. Your lab is where you build real skills, this step already sets you apart and you will find your learning accelerates as you build and troubleshoot a home lab.
What you need to get started:
- VirtualBox or VMware (free for personal use)
- Kali Linux for security tooling
- Vulnerable targets: Metasploitable, DVWA, VulnHub machines
- Isolated network configuration
Further resources:
The updated Practice Lab Setup Guide walks through complete configuration and different options for lab setups.
Docker for cybersecurity offers an alternative for spinning up environments quickly.
Try the session hacking demo and full code download
How to Document Your Cybersecurity Learning
Document every lab build, error message, and solution. This habit separates professionals from hobbyists.
Obsidian is a free, local-first note-taking tool that excels at connecting ideas. I have been using it for a few years and absolutely love it. Try it out, try a few out and see which app works for you. Use it to document commands, problems solved, and concepts learned. Link related notes together. See Building a Second Brain for Cybersecurity for ideas on how to push note taking to another level.
Phase 2: Building Core Security Skills (Month 3-6)
Phase 2 develops practical capabilities that make you useful on a security team. This is also when you choose your specialisation.
Scripting and Automation for Security
Security work involves repetitive tasks. Scripting multiplies your effectiveness.
Python focus areas:
- Reading and modifying existing security scripts
- Automating repetitive tasks
- Parsing logs and data files
- Interacting with APIs
- Building small tools that solve specific problems
You don't need to be a developer. You need to automate workflows and extend existing tools. This is also where AI tools like Claude code become a powerful co-pilot to understand, craft, and debug scripts.
Secondary scripting: Bash for Linux, PowerShell for Windows.
Hands-On Practice
CTF Platforms: Start with TryHackMe (guided rooms) or PicoCTF (beginner-focused). Progress to HackTheBox (realistic machines) and VulnHub (offline VMs). Document every challenge. Writeups become portfolio pieces.
Lab Progression: Build skills progressively in your home lab:
- Reconnaissance - Scan your lab network with Nmap. Identify services, versions, potential vulnerabilities.
- Traffic analysis - Capture packets with Wireshark while performing activities. Learn what normal and malicious traffic looks like.
- Log analysis - Enable logging on lab VMs. Correlate log events to actions manually before adding tooling.
- Detection - Deploy ELK Stack or Wazuh. Forward logs, build dashboards, create alerts.
- Attack and detect - Attack your own infrastructure, then find evidence of each phase in your logs.
The ELK Stack Security Monitoring Tutorial covers SIEM setup. Most entry-level jobs are defensive. Learning to catch attackers is as valuable as learning to emulate them.
Additional platforms: LetsDefend (SOC practice), CyberDefenders (DFIR challenges), PentesterLab (web app security).
Choosing Between Blue Team, Red Team, and GRC
By Month 6, choose your focus for the next 6-12 months:
Blue Team (Defensive): SOC analyst, threat hunter, incident responder. Focus on monitoring, detection, response.
Red Team (Offensive): Penetration tester, vulnerability researcher. Focus on finding and exploiting weaknesses.
GRC (Governance, Risk, Compliance): Compliance officer, risk manager, auditor. Focus on frameworks, policies, business risk.
Many practitioners move between tracks throughout careers. Choose a focus, not a permanent decision.
Phase 3: Specialisation and Advanced Skills (Month 6-12)
Phase 3 develops depth in your chosen track. These skills differentiate you from other candidates.
Blue Team Track
SIEM and Log Analysis: Master Splunk, ELK Stack, or Microsoft Sentinel. Write detection rules, correlate events, investigate alerts.
Threat Detection: Alert triage, IOC analysis, threat hunting, MITRE ATT&CK mapping.
Incident Response: IR procedures, evidence preservation, timeline reconstruction, reporting.
EDR: Understanding capabilities, alert investigation, endpoint forensics basics.
Red Team Track
Reconnaissance: Passive and active information gathering, service enumeration, attack surface mapping.
Web Application Security: OWASP Top 10, manual testing, Burp Suite, common exploitation.
Exploitation: Vulnerability validation, Metasploit, post-exploitation, privilege escalation.
Reporting: Clear, actionable vulnerability reports. This skill often determines who gets hired.
GRC Track
Frameworks: Deep familiarity with NIST CSF, ISO 27001, SOC 2, plus sector-specific (PCI-DSS, HIPAA). 27% of entry-level GRC postings prioritise framework knowledge over coding (Sprinto, 2025).
Risk Assessment: Risk identification, quantitative and qualitative methods, risk registers, communicating to stakeholders.
Policy and Compliance: Policy development, control mapping, audit preparation, vendor risk management.
In-Demand Cybersecurity Skills
The ISC2 2025 study identified critical gaps that will persist into 2026:
- AI Security (41% gap) - AI/ML vulnerabilities, prompt injection, model security
- Cloud Security (36% gap) - AWS, Azure, GCP security services. 88% of enterprises use a hybrid infrastructure (Cloud Security Alliance)
- Risk Assessment (29% gap) - Quantifying and communicating risk to leadership
- Application Security (28% gap) - Secure coding, code review, (see DevSecOps spotlight)
Target cloud fundamentals regardless of your track, the following article provides insights into the changing threat landscape monitoring the landscape is a good way to understand which skills might be in demand.
Soft Skills for Cybersecurity
Communication: Explain technical issues to non-technical audiences. Practice clear incident summaries.
Problem-solving under pressure: CTFs and complex lab scenarios build this muscle.
Phase 4: Getting Your First Cybersecurity Job
Technical skills open doors. Phase 4 converts capabilities into job offers.
Finding information independently is a core competency. The field moves too fast for any course to stay current.
Stay current: Follow threat intelligence feeds. Build RSS feeds and alerts for your speciality.
Experiment constantly: Most tools are free. Download them, break things in your lab.
Ask good questions: Demonstrate what you've tried before asking for help. The community helps those who help themselves.
Which Cybersecurity Certification Should You Get First?
Certifications prove baseline knowledge and pass HR filters. Choose based on track, target roles, and local market.
Industry Standard Certifications (Global Recognition)
| Track | Entry Level | Next Level | Certification Body |
|---|---|---|---|
| Foundation | CompTIA Security+ | CySA+ or cloud cert | CompTIA (est. 1982) |
| Blue Team | CompTIA CySA+ | GIAC GCIH, GCIA | CompTIA / SANS Institute |
| Red Team | eJPT | OSCP | INE / Offensive Security |
| Cloud | AWS Security Specialty, AZ-500 | CCSP | AWS, Microsoft, ISC2 |
| GRC | CISA, ISO 27001 Lead Implementer | CRISC, CISM, CISSP | ISACA (est. 1969), ISC2 |
About the Certification Bodies:
- ISC2 - Global nonprofit, 160,000+ members. CISSP is the gold standard for senior roles.
- ISACA - Established 1969, gold standard for audit/GRC with CISA, CRISC, CISM.
- SANS/GIAC - Premium certifications. Expensive but highly respected.
- Offensive Security - OSCP is the industry benchmark for penetration testing since 2006. Practical 24-hour exam.
- CompTIA - Vendor-neutral baseline. Security+ often the minimum for entry-level.
- INE - eJPT is a respected practical entry point for offensive security.
Practical Certifications (Hands-On Focus)
| Certification | Focus | Notes |
|---|---|---|
| OSCP | Penetration testing | 24-hour practical exam. Gold standard for offensive roles. |
| eJPT | Entry penetration testing | Practical format. Good stepping stone to OSCP. |
| GIAC certs | Various specialisations | Practical components. Premium pricing, highly respected. |
| CREST CRT/CCT | Penetration testing | Required for UK government testing. Recognised in UK, Australia, Asia. |
Emerging Practical Certifications
These are newer, gaining community traction, but may not be recognised by all HR departments:
| Certification | Provider | Notes |
|---|---|---|
| BTL1 | Security Blue Team | Launched ~2020. Excellent practical blue team content. Growing recognition. Good complement to CySA+. |
| PNPT | TCM Security | Well-respected founder. Includes report writing. May need explanation to some employers. |
Regional Considerations
- United Kingdom: NCSC Certified Training and CHECK for government work. CREST (CRT, CCT) for penetration testing.
- European Union: ISO 27001 certifications valued due to GDPR alignment. Privacy certifications (CIPP/E, CIPM) increasingly relevant.
- Germany: BSI certifications for government-adjacent work. ISO 27001 valued across industries.
- United States: Security+ meets DoD 8570/8140 for government and defence contractors.
- Australia/New Zealand: IRAP for government work. CREST and OSCP for offensive roles.
Framework-Specific Certifications
| Framework | Certifications |
|---|---|
| ISO 27001 | Lead Implementer, Lead Auditor (PECB, BSI, IRCA) |
| PCI-DSS | PCIP, QSA certification |
| Privacy/GDPR | CIPP/E, CIPM (IAPP) |
Building a Cybersecurity Portfolio
Your portfolio proves you can do the work.
GitHub: Scripts and tools, CTF writeups, lab configurations, detection rules.
Blog or documentation: Technical tutorials, project documentation, challenge writeups.
Include: Home lab architecture, CTF solutions with methodology, tools built or modified, detection rules created.
Professional Networking for Cybersecurity
Most jobs aren't posted publicly. Referrals bypass HR filters.
Organisations: ISC2, ISACA, ISSA (all have local chapters with events).
Events: BSides conferences (community-organised, accessible), local meetups, OWASP chapters.
Online: LinkedIn engagement, Discord communities (TryHackMe, HackTheBox).
Give before you ask. Share resources, answer questions, help others.
Can You Get into Cybersecurity with No IT Background?
Don't force a jump to "security analyst" from zero.
IT roles as stepping stones: Helpdesk, network admin, support engineer build paid experience while you develop security skills.
I started on frontline helpdesk, resolving tickets daily. That foundation made everything that followed easier.
The vendor backdoor: Solutions Engineer or Customer Success at security vendors provides access to enterprise tools and training. If direct security roles aren't opening, vendor-side offers an alternative path.
This is just the starting point the career guide will help you map out the complete journey, how to get hired, skills to focus on , practical lab exercises, using ai prompts to learn faster, interview preparation, resources and much more.
Download the free 58-page Cybersecurity Career Guide Detailed role tracks, lab ideas, AI prompts, portfolio advice, interview prep, and job-readiness guidance.
Frequently Asked Questions
How long does it take to learn cybersecurity?
With focused effort, you can become job-ready in around 12 months. The first 3 months build foundations (networking, Linux, lab setup). Months 3-6 develop core skills, and months 6-12 focus on specialisation and portfolio building.
The key is not time, it is consistency and hands-on practice. People who build labs and document their work progress much faster than those who only consume content.
Do I need a degree for cybersecurity?
No. Most employers prioritise demonstrable skills, certifications, and practical experience over formal education. A strong home lab, portfolio, and documented projects often carry more weight than a degree.
However, degrees can still help with visa requirements and certain government or enterprise roles.
What cybersecurity certification should I get first?
CompTIA Security+ is the most common starting point. It provides a recognised baseline and helps pass HR filters.
After that, choose based on your path:
- Blue team: CySA+ or BTL1
- Red team: eJPT → OSCP
- GRC: CISA or ISO 27001Certifications support your profile, but they do not replace hands-on skills.
Can I learn cybersecurity with no IT background?
Yes, but expect to spend more time on foundations. Networking and Linux will take longer without prior exposure.
Many successful professionals started from zero. The difference is they built practical experience early through labs, projects, and consistent practice.
What is the best cybersecurity career path for beginners?
SOC Analyst is the most common entry point because of demand and accessibility. These roles focus on monitoring, detection, and incident response.
From there, you can specialise into threat hunting, incident response, red team, cloud security, or GRC depending on your interests.
How much do entry-level cybersecurity jobs pay?
Salaries vary by region and role.
- UK: £25,000–£35,000 typical entry-level SOC roles
- US: $50,000–$70,000 common starting range Higher salaries come with specialisation, cloud skills, or experience. Remote work has increased opportunities but also competition.
Should I learn programming for cybersecurity?
You do not need to be a software developer, but scripting is essential. Python is the most useful language for automation, data parsing, and tooling.
Focus on reading, modifying, and debugging scripts rather than building everything from scratch. AI tools can accelerate this, but you still need to understand what the code is doing.
Is cybersecurity a good career in 2026?
Yes, but it is becoming more competitive at entry level. The ISC2 2025 study shows 59% of organisations report critical skills shortages, but they are looking for people who can contribute quickly.
The opportunity is strong if you focus on practical skills, build a portfolio, and demonstrate real capability, not just certifications.
What should I focus on first in cybersecurity?
Focus first on networking fundamentals, Linux basics, and setting up a home lab. These foundations apply across every cybersecurity role. Alongside technical skills, build awareness of security frameworks and benchmarks such as NIST, ISO 27001, and CIS. These are used in real environments and help you understand how organisations manage risk, not just how tools work
Your 12-Month Action Plan
Use the free 58-page Cybersecurity Career Guide
This contains detailed role tracks, lab ideas, AI prompts, portfolio advice, interview prep, and job-readiness guidance and will help you work through each phase.
Phase 1 (Month 1-3): Foundations
Set up home lab and knowledge base. Master networking fundamentals and Linux. Learn Nmap and Wireshark. Join one security community. Learn about threat actor tradecraft.
Phase 2 (Month 3-6): Core Skills
Develop Python scripting. Complete 20+ CTF challenges. Build SIEM in your lab. Choose specialisation track.
Phase 3 (Month 6-12): Specialisation
Deep dive into track-specific skills. Build portfolio projects. Add cloud security fundamentals. Start certification preparation.
Phase 4 (Month 12+): Career Launch
Complete certification. Publish portfolio. Activate professional network. Apply strategically.
For the 18 skills that separate top performers, see the Cybersecurity Career Playbook.
This roadmap gets updated as the skills landscape shifts. Subscribers receive notifications when major changes happen, plus weekly practical security content.
Last updated: April 2026
References and Sources
- ISC2. (2025). 2025 Cybersecurity Workforce Study. Survey of 16,029 cybersecurity professionals collected May–June 2025. 59% of teams report critical or significant skills shortages, up from 44% in 2024. 88% have experienced at least one significant security consequence due to skills deficiencies.
- ISC2. (2025). 2025 Cybersecurity Hiring Trends Report. Survey of 929 hiring managers across Canada, Germany, India, Japan, the UK, and the US. 56% say training entry-level professionals to handle tasks independently typically takes 4–9 months. 90% prioritise hands-on IT experience; 89% prioritise certifications over candidates with education alone.
- W3Techs. (March 2026). Usage Statistics of Operating Systems for Websites. 96.3% of the top one million web servers run on Linux. Live data updated monthly.
- Cloud Security Alliance & Tenable. (2025). The State of Cloud and AI Security 2025. Survey of 1,000+ professionals. 82% of organisations operate hybrid cloud infrastructure. 63% use more than one cloud provider. Identity and access management identified as the top cloud security risk.
- ISC2. (2025). 2025 Cybersecurity Workforce Study. AI security identified as the single largest skills gap, cited by organisations alongside cloud security, risk assessment, and application security as the top four critical shortfalls.




Member discussion