Cybersecurity Compliance Career Guide 2026

May 2026
Most career advice treats compliance as the boring corner of cybersecurity. Twenty years working with enterprise security teams has taught me the opposite.
The compliance and framework specialists who can translate audit language into operational reality are some of the most influential people in any security organisation. They decide which controls get prioritised, which gaps get funded, and which arguments the security team can win with the board.
The cybersecurity skills shortage in 2026 is not a headcount problem. It is a capability mismatch, with 59% of security teams reporting critical or significant skills gaps, up 15% on the previous year (ISC2, 2025).
For compliance and framework professionals specifically, the demand is sharper than the headline numbers suggest. CyberSeek's June 2025 mapping to the NICE Workforce Framework recorded 355,590 job postings in the Oversight and Governance category, the single largest category in the dataset, ahead of Implementation and Operation at 335,993 and Design and Development at 331,644 (CyberSeek, June 2025).
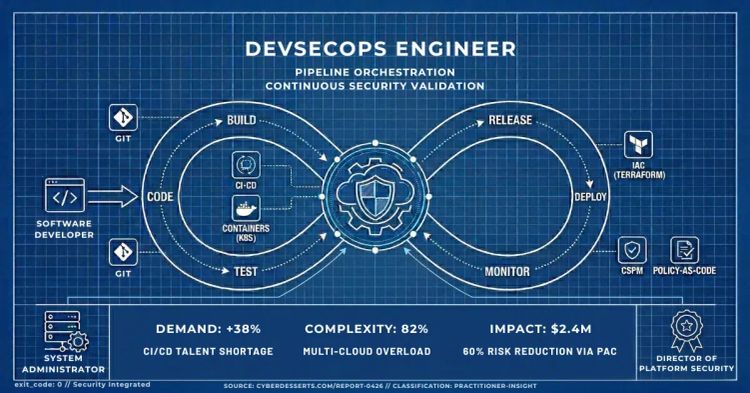
April's report covered DevSecOps in depth. This month moves from how secure software gets built to how organisations prove they are managing security at all.
The work sounds dry on paper. It turns out to be one of the most strategic career tracks in the field.
- 355,590 Oversight and Governance job postings, the largest single category in the U.S. cybersecurity workforce data (CyberSeek, June 2025) - Top five SOC hiring criteria are all nontechnical and the same pattern holds for compliance hiring (ISC2, 2025) - The skill that compounds: translating framework controls into operational evidence auditors will accept
How to Build a Cybersecurity Compliance and Frameworks Career in 2026
The route into compliance is one of the most under-rated entry paths into cybersecurity. IT auditors, technical writers, project managers from regulated industries, and systems administrators with documentation discipline all bring transferable skills the field needs. You do not have to start with a technical security background to be valuable here.
Entry-level work is structured and document-heavy. You learn to read NIST CSF 2.0, CIS Controls v8, and NIST 800-53 as the underlying logic of how frameworks specify their requirements.
You sit in audit prep meetings. You build asset inventories that auditors will accept and identify control gaps that the security team will need to close.
The tooling at this stage is deliberately light: NIST CSF worksheets, risk register templates, control matrices in Excel or Confluence, and shared documentation platforms. The value you add is not technical depth. It is the discipline to make controls legible to people who do not write them.
Mid-level is where the role gets demanding and where most weak compliance careers stall. You are mapping controls across multiple frameworks, running gap assessments, managing SOC 2 Type II audits, and learning the language of risk-based prioritisation. Tools like Archer, ServiceNow GRC, and OneTrust become daily companions.
What separates strong from mediocre at this level is the ability to take a framework requirement and produce a control implementation that both passes the audit and survives an incident. That gap, between the words in NIST 800-53 and the SIEM rule that proves the control is operating, is where the career compounds.
A day in the life at mid-level. The morning is reviewing evidence collection automation for an upcoming SOC 2 audit, identifying a sample gap in the access review records and chasing the IT team for remediation. Mid-morning is a working session with a security engineer to translate a NIST CSF Detect function into a Splunk detection that produces audit-acceptable output.
The afternoon is a vendor risk questionnaire for a new SaaS procurement, followed by the executive summary of a SOC 2 readiness assessment. The work is conversational and political as much as technical.
Senior compliance and framework specialists move into program design. You build the security program. You handle multi-framework compliance for organisations that need PCI-DSS, HIPAA, SOC 2, and ISO 27001 simultaneously.
You report to the board. You quantify risk in financial terms using FAIR-based models and make the case for investment in language that finance understands (which sounds dry until you realise how few people in any organisation can do this credibly). The career also pivots cleanly into broader GRC leadership, CISO tracks, vCISO advisory, and regulatory strategy.
Where this path leads in three to five years. Senior compliance and framework specialists move into Head of GRC, vCISO, Director of Risk and Compliance, or CISO roles. The scarcest senior talent is people who can operate credibly with both engineering leadership and the regulators. If you can hold that bridge, the career ceiling is high.
For how compliance and frameworks sits alongside the other 14 cybersecurity domains, with the full role descriptions and entry requirements for each, see Cybersecurity Career Paths: Complete Guide for 2026.
Top Cybersecurity Skills Compliance and Frameworks Specialists Need in 2026
April's report covered the technical skills employers want across the field generally, including phishing detection, PowerShell analysis, EDR deployment, and detection engineering. The skills below are the ones that specifically compound in a compliance and framework career.
They are not survey-popularity rankings. They are the capabilities that translate framework language into evidence auditors accept and operational controls security teams can run in production.
Cross-Framework Mapping Across NIST, ISO 27001, and CIS Controls
NIST CSF 2.0 is the most transferable framework to learn first, and the one most organisations will use as the umbrella over their other compliance commitments. CIS Controls v8 sits underneath it as the operational layer.
NIST 800-53 provides the depth for federal and regulated industry work. ISO 27001 is the international counterpart and increasingly expected for any organisation operating outside the US.
Fluency means more than knowing the framework structure. It means being able to map a single business risk through to the controls in two or three frameworks at once, and produce the evidence requirements for each one without rebuilding the work three times.
The mature compliance specialist knows how the frameworks overlap, which controls trace cleanly to which audit assertions, and where the mapping breaks down. That last point matters because most compliance work is the gap between the words on the page and what the organisation can credibly demonstrate.
Risk Quantification Separates Mid from Senior
FAIR (Factor Analysis of Information Risk) is the model that takes the conversation from red-amber-green heatmaps to dollar figures the board can argue about. Practitioners who can build a quantified risk model and walk a CFO through the assumptions get hired into roles that red-amber-green practitioners do not.
The free resources from the FAIR Institute are the structured starting point. The CRISC certification covers similar territory from the ISACA side.
The skill that hiring managers test for is not the maths. It is the ability to defend the assumptions when a finance director pushes back on the numbers.
Return on Security Investment (ROSI) is the companion model to learn alongside FAIR. The calculation pairs the cost of a control against the dollar reduction in annual loss expectancy that control produces. Where FAIR teaches you to quantify the risk, ROSI translates the investment decision into the same comparative framing boards already apply to business interruption insurance and capital expenditure.
Sitting above both is the Security Metric Maturity Model, a five-tier progression from operational data through to predictive metrics. The senior compliance specialist who reports at the strategic and predictive tiers gets a different reception from the board than the one handing across raw activity counts.
For the full breakdown of how to translate compliance metrics into language executives understand, including ROSI calculation and the maturity model framework, see Information Security Metrics for Executives: How to Close the Value Gap.
Control Mapping and Evidence Automation
The single highest-leverage mid-career skill is the ability to map a control once and produce evidence for multiple framework assertions from the same source data. Most organisations re-do this work for every audit cycle. The compliance specialist who builds the mapping infrastructure once, and automates the evidence collection through ServiceNow GRC or Archer or a custom pipeline, saves the organisation significant time and gets noticed for it.
Evidence collection automation is no longer an aspiration. Tools like Drata, Vanta, and Secureframe have made continuous compliance the standard expectation for SOC 2 and ISO 27001 programs. Familiarity with at least one of these, even from the candidate-evaluation side, is increasingly a hiring criterion.
Cloud Compliance Translation
Most audit evidence now lives in cloud control planes. AWS Config, Azure Policy, GCP Security Command Center, and CloudTrail are where the compliance specialist of 2026 finds the data auditors want.
Translation here means being able to look at a NIST 800-53 control like AC-2 (Account Management), identify the cloud control plane signal that proves it is operating, configure the logging and alerting to capture that evidence, and document the chain of custody back to the control assertion. Practitioners who can do this across multi-cloud environments are scarce. Hiring demand is sharper than the role titles suggest.
Regulatory Tech Literacy: EU AI Act, SEC Disclosure, CRA
The regulatory picture shifted materially in the last 18 months and the compliance specialists who understand the new instruments have outsized career value. The EU AI Act enforcement begins in August 2026 and applies to any organisation deploying AI systems in the EU market.
The SEC cyber disclosure rules are now in force for public companies. The EU Cyber Resilience Act (CRA) is moving toward enforcement in 2027 and applies to any product with digital elements.
Each of these is appearing in audit scopes. None of them are well-covered in traditional GRC training. The compliance specialist who can read the regulation, map the obligations to existing framework controls, and identify the new evidence requirements is solving a problem the market has only just started to feel.
Soft Skills Cybersecurity Hiring Managers Prioritise
The 2025 ISC2 Workforce Study asked hiring managers to name the skills they prioritise. The top five were all nontechnical: problem solving (29%), collaboration (24%), communication (22%), willingness to learn (20%), and strategic thinking (16%) (ISC2, 2025).
Not cloud security, not SIEM experience, not certifications. Soft skills, first through fifth.
That finding deserves a moment of attention because it changes how compliance and framework candidates should prepare. The technical floor for the role is real, but it is the floor. The skills that get you hired sit above it.
I put the question directly to SOC hiring managers earlier this year for What SOC Hiring Managers Test For In Interviews. The findings translate directly to compliance hiring with one amplification. Communication weight is higher in compliance work because the role is structurally a translation job, between auditors and engineers, between regulators and the board, between framework language and operational reality.
Omer Malik, CEO at ORM Systems, puts it in operational terms. Put a candidate with strong credentials in front of a realistic scenario and ask them to reason out loud, and the gap between certified and capable shows up inside the first few minutes.
For compliance candidates, the equivalent is being asked to explain a control failure to a non-technical executive in two minutes. Candidates who launch into framework references and acronyms lose the room. Candidates who translate cleanly into business consequences win the role.
Chandra Sekhar Muppala, Senior Manager for Cybersecurity and Operations at Infosprint Technologies, points to operational depth as the line that separates strong candidates. The compliance equivalent is the candidate who has run an audit cycle end to end, sat in front of an auditor, and defended their evidence narratives under scrutiny. That experience carries something a certification cannot document.
Ilia Mogilin, Security Operations Engineer, treats self-directed learning as the strongest forward indicator of a candidate's trajectory. For compliance, this shows up in the candidate who taught themselves the EU AI Act ahead of the audit cycle, not after it appeared as a finding. The compliance specialists who progress fastest are the ones who bring regulatory change into their organisation before the auditor does.
Curiosity emerged as the X-factor across all three conversations. The compliance reading of curiosity is the analyst who notices an access review with no exceptions for six consecutive months and asks why, then discovers the reviewer has been rubber-stamping without checking the underlying data. Calm under pressure, willingness to learn, and the discipline to question quiet signals are the soft skills that compound across both SOC and compliance careers.
Best Cybersecurity Certifications for Compliance and Frameworks Specialists
Certifications buy three things in this field: permission to clear the HR filter, signal of credibility with hiring managers, and proof of specific competency. CompTIA Security+ is the entry-level credential that gets past most HR filters, and ISO 27001 Foundation adds the framework signal that opens doors outside the US where ISO is the default standard. CISA is the cleanest mid-career opener into audit work and Big 4 advisory tracks, with CRISC the equivalent for enterprise risk management roles. At senior level, CISSP earns its keep as the breadth signal most leadership job postings screen against, with CGEIT specialising that signal toward IT governance and board-facing work. The full progression with hours, fees, and renewal burden sits in the Cybersecurity Skills Roadmap for those weighing the investment side. The contrarian observation worth holding onto: hiring managers in 2026 increasingly prioritise demonstrated portfolio work over stacked credentials, and a documented audit you ran or a control mapping you built will move a mid-career conversation further than a second certification (ISC2, 2025).
Cybersecurity Tools for Compliance and Frameworks Professionals in 2026
April covered the broad tooling stack across the cybersecurity field, including Wireshark, Nmap, Sysmon, and the detection engineering toolchain. The tools below are the ones that specifically matter for compliance and framework work, and the ones hiring managers expect candidates to have at least operational familiarity with by mid-career.
Entry-Level: Documentation Discipline and Framework Tools
NIST CSF worksheets, the CIS Controls v8 self-assessment template, and the NIST 800-53 control catalog are all free. They are the conceptual starting point. Build the habit of reading framework language critically, not as compliance text but as design specifications.
Confluence, SharePoint, or Notion for control documentation and audit evidence repositories. The platform matters less than the discipline. Compliance careers stall when documentation is treated as administrative overhead instead of the core deliverable.
For risk registers, basic spreadsheet skills are sufficient at entry level. Pivot tables, conditional formatting, and the ability to maintain a clean control-to-risk mapping in Excel is the underlying skill before moving to GRC platforms.
Mid-Level: GRC Platforms and Cloud Compliance
Archer (now Archer Technologies, post-divestiture from RSA) and ServiceNow GRC are the two dominant enterprise GRC platforms. Working familiarity with at least one of these is increasingly a hiring criterion. The conceptual model is the same across both: risk registers, control libraries, audit evidence collection, and continuous monitoring workflows.
OneTrust covers privacy program management, third-party risk assessment, and increasingly AI governance modules. For organisations with significant privacy regulation exposure (GDPR, CCPA, the UK Data Protection Act), OneTrust is the default platform.
For cloud compliance, the practitioner toolkit has matured significantly. Prowler is the open-source AWS auditing tool that maps directly to CIS Benchmarks and AWS Foundational Security Best Practices.
ScoutSuite covers multi-cloud auditing across AWS, Azure, and GCP. Steampipe lets you query cloud control planes with SQL, which is useful for building custom evidence queries that go beyond what the native tooling produces.
Drata, Vanta, and Secureframe sit in the continuous compliance category specifically targeted at SOC 2 and ISO 27001 programs. Even if your organisation does not use one, hiring conversations will reference them.
Senior-Level: Policy-as-Code and Risk Quantification
Open Policy Agent (OPA) and Conftest are the open-source policy-as-code tools that let compliance specialists embed control checks directly into CI/CD pipelines and infrastructure deployment workflows. At senior level, the goal is to move beyond control matrices toward continuous compliance architecture where the framework requirements run as code alongside the systems they govern.
For risk quantification, the FAIR Institute provides free tooling and training. Commercial platforms include RiskLens and Safe Security, which automate the FAIR model at enterprise scale. Senior compliance specialists who can build and defend quantified risk models in a boardroom conversation have a skill that almost no certification trains.
GRC dashboards and executive reporting templates are the senior-level output. Tools matter less than the underlying ability to take a complex compliance posture and present it to a board in 90 seconds with credibility intact.
Security Trends Shaping Cybersecurity Careers in 2026
Four trends are reshaping what employers hire compliance and framework professionals for. Each one has a clear skills implication.
AI Security Jobs in 2026: EU AI Act and Governance Frameworks
AI is reshaping cybersecurity careers from both sides. ISC2 ranks AI/ML as the single most-needed skill area in the 2025 study, and 72% of respondents expect AI to require more strategic security mindsets (ISC2, 2025). For compliance and framework specialists, the more immediate signal is regulatory.
The EU AI Act enforcement begins in August 2026. The NIST AI Risk Management Framework is the closest US equivalent and is appearing in federal procurement requirements.
Both are now showing up in audit scopes. The compliance specialist who can read the regulation, map the obligations to existing controls under NIST CSF or ISO 27001, and identify the new evidence requirements is solving a problem most organisations have only just started to feel.
The OWASP LLM Top 10 and MITRE ATLAS are the technical references that bridge the regulatory side to the operational side. Familiarity with both is the differentiator for compliance specialists working with AI deployments.
Cloud Security: Where Audit Evidence Now Lives
ISC2 ranks cloud security as the second-most demanded skill in 2025, with demand growing six percentage points year over year (ISC2, 2025). For compliance and framework careers specifically, the cloud overlap is the binding constraint. Most audit evidence now lives in cloud control planes, and the practitioner who can read CloudTrail or Azure Activity Log fluently can build evidence collection workflows that the practitioner who only reads control matrices cannot.
Kubernetes hardening, container security baselines, and serverless audit logging are increasingly named in job postings as specific requirements rather than implied background knowledge. CIS Benchmarks for AWS, Azure, GCP, and Kubernetes are the operational starting point.
Supply Chain Security and SBOM Regulatory Compliance
Software supply chain security has moved from emerging concern to standard compliance requirement. The EU Cyber Resilience Act (CRA), the SEC cyber disclosure rules, and Executive Order 14028 in the US have all elevated software supply chain to a board-level conversation.
For compliance specialists, the practical skills are SBOM literacy (CycloneDX is the dominant open standard), third-party risk assessment frameworks, and the mapping between supply chain controls in NIST 800-161 and the older controls in NIST 800-53. The role blends GRC knowledge with technical software security awareness, which makes it a natural pivot for compliance specialists who want to move closer to engineering.
CIS Control 15 (Service Provider Management) and CIS Control 2 (Software Asset Inventory) are now baseline requirements in most modern programs, not aspirational targets.
Zero Trust: Identity-Centric Compliance Architecture
Zero Trust has moved from concept to baseline requirement in most enterprise security strategies, and the framework implications are significant. NIST 800-207 is the canonical reference. The compliance specialist who can take a Zero Trust maturity model and map it cleanly into existing controls under NIST CSF 2.0, ISO 27001, or CIS Controls v8 brings a skill that most legacy compliance teams do not yet have.
For practitioners moving into Zero Trust work from a compliance background, the early wins are usually in identity-centric control mapping, conditional access policy design, and identifying where existing identity controls fall short of the maturity model. The book Zero Trust Networks 2nd edition by Evan Gilman and Doug Barth is the practitioner's read, not the vendor's white paper.
Continuous Compliance and Audit Automation
The fastest-growing operational expectation in 2026 is continuous compliance. The model has shifted from quarterly audit cycles with point-in-time evidence to continuous evidence collection running against framework controls in real time. Drata, Vanta, and Secureframe have made this the default for SOC 2 and ISO 27001 programs in mid-sized organisations.
For senior compliance specialists, the skill is architectural. Building a continuous compliance pipeline that ingests evidence from cloud control planes, IAM systems, ticketing platforms, and security tools, and produces audit-ready output without quarterly fire drills, is the senior compliance deliverable of 2026. Practitioners who can design this architecture, not just operate within it, are scarce and well compensated.
Continuous compliance is the audit-side expression of a broader operational shift. The conceptual frame underneath it is Continuous Threat Exposure Management, the Gartner-introduced approach from 2022 that treats every exposure category as part of the same risk picture: software vulnerabilities, identity misconfigurations, control failures, and process gaps all in scope, not just CVEs.
For compliance and framework specialists, CTEM matters because its validation phase answers a question most audit cycles cannot reach. Validation tests whether a control performs as intended in the environment it has been deployed into, not just whether it appears in the architecture diagram.
The five CTEM stages, scoping, discovery, prioritisation, validation, and mobilisation, give framework programmes an operational layer that maps usefully onto NIST CSF 2.0's Identify, Protect, Detect, Respond, and Recover functions, though not as a one-to-one mapping. The compliance specialists who can speak both languages, audit assertion and exposure validation, are increasingly the candidates senior hiring managers are looking for.
For the full operating model and how CTEM differs from traditional vulnerability management, see What is CTEM? Continuous Threat Exposure Management.
Breaking Into Cybersecurity Compliance and Frameworks
The opportunity is real. The 355,590 Oversight and Governance job postings in CyberSeek's June 2025 data make this the single largest category in the U.S. cybersecurity workforce, and 59% of teams report critical skills gaps they cannot fill (CyberSeek, June 2025; ISC2, 2025). The entry point is more accessible than most cybersecurity domains because the technical floor is lower at the start.
First steps that work. Read NIST CSF 2.0 cover to cover. It is free, well-documented, and the most transferable framework you can learn first.
Add CompTIA Security+ to demonstrate technical baseline knowledge, and at least one read of a published SOC 2 Type II report (most cloud vendors publish theirs publicly) to understand how controls translate into audit evidence. ISO 27001 Foundation is the natural next step if you want lifetime validity at low cost.
Transferable backgrounds that work. Project management in regulated industries (finance, healthcare, pharma) transfers directly. Technical writing transfers directly.
IT audit experience is the cleanest crossover. Systems administration with documentation discipline transfers well, particularly into the cloud compliance translation work. If you have experience explaining technical work to non-technical stakeholders in any prior role, you have the core skill.
Common mistakes. Treating compliance as administrative overhead instead of operational design. The mature practitioner does not see frameworks as a paperwork exercise.
They see them as the specification for what good security looks like, written in a language the board can ratify. Candidates who carry the paperwork mindset into interviews are easy to identify and easy to filter out.
Skipping the technical layer entirely. Even at entry level, you need to understand how a control like AC-2 (Account Management) gets implemented and evidenced in a modern cloud environment. The compliance specialist who can only read the control text and not the cloud signal that proves it is operating gets stuck early.
Resources worth your time.
Measuring and Managing Information Risk: A FAIR Approach by Jack Freund and Jack Jones is the practitioner reference for quantified risk. It teaches the methodology, not just the framework.
The CISO Evolution by Matthew K. Sharp and Kyriakos Lambros covers the leadership trajectory that compliance and framework specialists often follow into senior roles. Read it before your first senior interview.
For the broader cybersecurity reading path mapped to career stage and domain, Best Cybersecurity Books 2026 covers the canonical recommendations.
For the full picture of how compliance and frameworks sits alongside the other 14 cybersecurity domains, see Cybersecurity Career Paths: Complete Guide for 2026.
What the May 2026 Cybersecurity Job Market Tells You
The skills gap framing is now the dominant signal in cybersecurity workforce data. 59% of teams report critical or significant skills deficiencies and the focus has shifted from headcount to capability (ISC2, 2025). For compliance and framework specialists, the demand is sharper than the headline numbers suggest because the Oversight and Governance category is the largest single segment of U.S. cybersecurity job postings.
The translation skill is what compounds. Frameworks describe what good security looks like on paper. The careers that compound over time belong to the people who can make them work in practice, who can take a NIST 800-53 control and produce evidence the auditor will accept, who can read the EU AI Act and identify the new control requirements before the audit cycle does, who can sit between the engineers and the board and explain both sides accurately.
Two resources to act on:
For mapping your current skills against the full set of cybersecurity career paths, the Cybersecurity Skills Roadmap covers the progression from entry level through senior roles.
To see how compliance and frameworks sits alongside the other domains, Cybersecurity Career Paths: Complete Guide for 2026 covers the full domain set with role descriptions, entry requirements, and salary ranges.
I have watched compliance functions treated as a paperwork team. I have watched the same teams become the people the CISO calls first when the EU AI Act audit hits or the SEC disclosure clock starts running.
Same role. Different reception.
The difference is whether anyone in the team can translate the framework into something operational when the board needs an answer that holds up.
Be the person who can.
References and Sources
- ISC2. (2025). 2025 ISC2 Cybersecurity Workforce Study. Data collected May/June 2025; 16,029 respondents. Key findings: 95% report at least one skills deficiency (up 5% from 2024); 59% cite critical or significant skills gaps (up 15% from 2024); top five hiring manager priorities are all nontechnical: problem solving (29%), collaboration (24%), communication (22%), willingness to learn (20%), strategic thinking (16%); AI ranked as a critical skills deficiency area; 72% expect AI to require more strategic security mindsets; ISC2 did not publish a headline workforce gap estimate in 2025, noting that skills shortages are a more pressing measure than headcount.
- CyberSeek. (June 2025). CyberSeek Cybersecurity Workforce Data and NICE Framework Mapping. Key findings: 514,000 U.S. cybersecurity job postings recorded in the prior twelve months; Oversight and Governance is the single largest NICE Workforce Framework category at 355,590 postings, followed by Implementation and Operation at 335,993 and Design and Development at 331,644.
- NIST. (2024). NIST Cybersecurity Framework 2.0. Reference framework. Available at https://www.nist.gov/cyberframework.
- CIS. (2024). CIS Controls v8. Reference framework with supporting self-assessment tools. Available at https://www.cisecurity.org/controls/.
- European Union. (2024). Regulation (EU) 2024/1689 (Artificial Intelligence Act). Enforcement of high-risk system requirements begins August 2026.
- European Union. (2024). Cyber Resilience Act (Regulation 2024/2847). Applies to products with digital elements; obligations begin to apply through 2027.
- U.S. SEC. (2023). Cybersecurity Risk Management, Strategy, Governance, and Incident Disclosure Final Rule. Public company disclosure requirements in force.
- FAIR Institute. Factor Analysis of Information Risk methodology. Reference model for quantified information risk. Available at https://www.fairinstitute.org/.
- CyberDesserts. CyberDesserts Threat Intelligence Knowledge Graph (cumulative, queried May 2026). Reference dataset of tracked threat actors, ransomware families, ATT&CK techniques, and public detection rule coverage. Technique counts are cumulative across all tracked actors and families and are not filtered to a single calendar year.
- CyberDesserts. (March 2026). What SOC Hiring Managers Test For In Interviews. Practitioner interviews with Omer Malik (ORM Systems), Chandra Sekhar Muppala (Infosprint Technologies), and Ilia Mogilin (Security Operations Engineer).
About This Report
Report month: May 2026. Spotlight domain: Compliance and Frameworks.
Workforce data is from the ISC2 2025 Workforce Study and CyberSeek June 2025 snapshot, the most recent primary publications available. Regulatory references are sourced from the published instruments.
The methodology is direct. Skills demand is derived from the intersection of attacker behaviour, regulatory change, and workforce data, not vendor marketing or survey self-reporting.
For compliance and framework careers, the most important career signal is not which framework is most popular but which combination of framework fluency, risk quantification, control mapping, and regulatory tech literacy compounds over a decade. This report is updated monthly with a rotating spotlight on a different cybersecurity career domain.
Some of the links included are Amazon affiliate links. If you buy through them I earn a small commission at no extra cost to you. It helps keep CyberDesserts free and independent.



Member discussion