Cybersecurity Career Report: April 2026
CyberDesserts | blog.cyberdesserts.com | April 2026
The cybersecurity skills shortage in 2026 is not a headcount problem. It is a skills-matching problem, and that distinction changes which career paths have the strongest hiring signal right now.
The ISC2 2025 Workforce Study puts a number on it: 95% of security teams report at least one skills deficiency, and 59% cite critical or significant gaps, a 15% increase from the previous year (ISC2, 2025). Notably, ISC2 dropped their headline workforce gap estimate from the 2025 study altogether. Their data showed the conversation had shifted from how many people are missing to which skills are missing. The most recent CyberSeek data, from June 2025, recorded 514,000 U.S. job postings. Those positions exist. The question is whether candidates have the right skills to fill them.
February's report covered cloud security in depth, and that report is here if cloud is your focus. This month's spotlight is DevSecOps, the domain that has become the connective tissue between software development speed and security accountability. We cover the full career arc from entry-level AppSec triage to senior product security leadership, map the skills employers are hiring for, and show how the threat landscape drives those hiring decisions.
- Four trends shaping hiring right now: AI security, cloud security, supply chain, detection engineering
- What gets you hired in a SOC has nothing to do with your technical skills
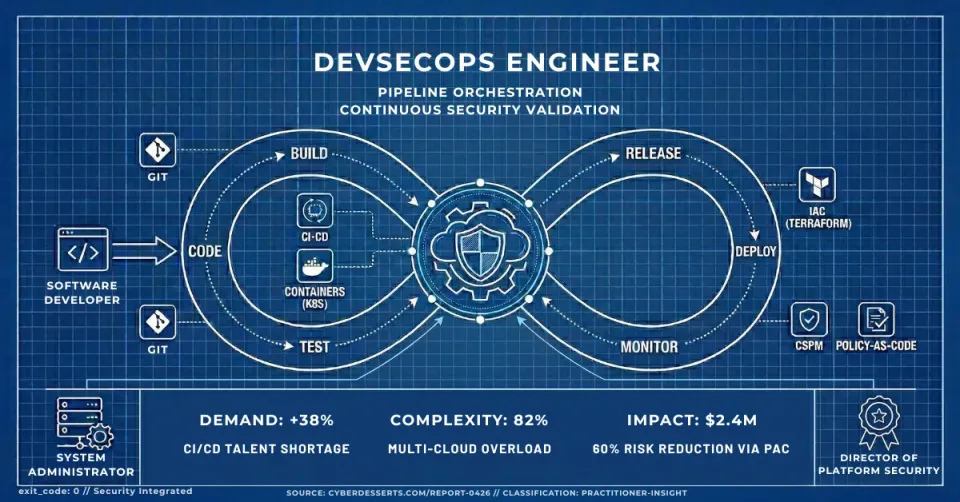
How to Become a DevSecOps Engineer in 2026
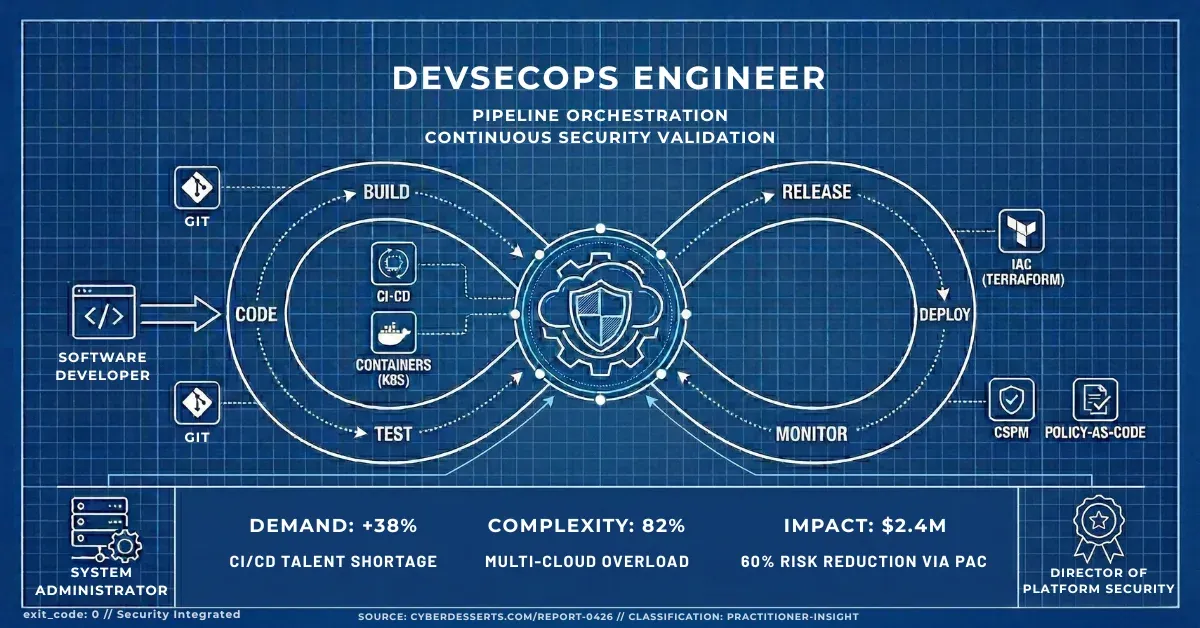
If you have a software development background, DevSecOps is the career transition with the shortest distance between where you are and where the jobs are. The CI/CD pipelines, Git workflows, and dependency management you already understand are the exact systems that security teams are trying to secure.
I came from a development background myself. Writing DLLs and niche business applications, including tax software for accountants, paid the bills but it was not where my head was. What changed everything was the debug and error handling work I ended up doing in direct communication with the helpdesk team and end users, trying to pinpoint runtime issues (you know, those annoying intermittent ones) as they were happening in the field. For the first time I was close to how the software was actually being used by real people with real problems. That feeling was completely different from anything I had experienced writing code in isolation. I followed it.
That path led me into frontline malware and antivirus helpdesk, and that DLL background turned out to matter more than I expected. Spotting DLL injection patterns is faster when you already understand how DLLs are structured and loaded at runtime. Developers bring that same advantage to DevSecOps: you already understand the systems you are trying to secure at a level most security practitioners learn after the fact, if they learn it at all.
The route into DevSecOps today is more direct than mine was. You do not need the frontline detour. But if you get the chance to spend time closer to how your software fails in the real world, take it.
The domain covers the intersection of software engineering, security tooling, and developer culture. That combination is rare, and employers pay for it. According to the CyberSeek NICE Workforce Framework mapping, Design and Development roles, the category covering DevSecOps and AppSec, account for over 331,000 job postings, trailing only Oversight and Governance (CyberSeek, June 2025).
What the role involves day to day. At the entry level, you spend your time configuring SAST tools like SonarQube and Snyk in CI/CD pipelines, triaging dependency vulnerabilities flagged by Snyk or Dependabot, and writing up findings for developers who didn't ask for your opinion. Container hardening is constant: Docker image scanning with Trivy or Docker Scout, reviewing base image choices, checking for secrets committed to Git with tools like GitGuardian. The OWASP Top 10 is your first language.
At the mid level, the work shifts from configuration to architecture. You run threat modelling sessions using STRIDE or PASTA, review security architecture for new features, and manage a software composition analysis (SCA) program across dozens of repositories. SBOM generation, IaC security scanning with Checkov or tfsec, and developer security training become your outputs. You're no longer just flagging problems. You're building the pipeline that prevents them.
A day in the life at mid-level. You start the morning reviewing a Semgrep CI report that flagged a potential SQL injection in a new microservice. You triage it, confirm it's exploitable, file a Jira ticket with remediation guidance, and schedule fifteen minutes with the developer to walk through the fix. The afternoon is a threat modelling session for an upcoming OAuth flow redesign. You close out by reviewing a Dependabot PR that auto-remediated a Log4j variant, confirming the fix doesn't break anything downstream.
Senior DevSecOps professionals build the program, not the tools. You design the product security program from scratch, define AppSec metrics and maturity models, run a security champion program across engineering teams, and manage the vulnerability disclosure process. The OWASP SAMM and BSIMM frameworks become your measurement tools. You report security posture to leadership.
Where this path leads in three to five years. Strong DevSecOps practitioners move into Head of Product Security, Application Security Director, or VP of Engineering Security roles. The scarcest talent at the senior level is people who can operate credibly with both engineering leadership and the CISO. If you can hold that bridge, the career ceiling is high.
For a broader look at how DevSecOps sits within the full cybersecurity ecosystem, the Cybersecurity Career Guide 2026 covers every major domain with the same practitioner perspective.
Cybersecurity Career Paths in 2026
The threat landscape shapes which skills each domain prioritises at each level. Phishing (T1566) is the most common initial access technique across tracked threat actors, which explains why every domain below includes email security or security awareness at entry level. Before going deeper on skills, here is how DevSecOps sits within the full domain landscape, and where the other 14 specialisations stand. The skills below are pulled from domain registries mapped to real job requirements.
| Domain | Entry-Level Differentiator | Mid-Level Differentiator | Senior-Level Differentiator |
|---|---|---|---|
| SOC | Alert triage, Windows Event Log analysis | KQL/SPL query writing, Sigma rule conversion | Detection engineering program design, SOAR playbooks |
| Threat Intel | IOC analysis, MITRE ATT&CK framework | YARA rule writing, Diamond Model analysis | Strategic threat assessments, intel program management |
| Incident Response | Evidence preservation, forensic imaging | Memory forensics, ransomware response playbooks | IR program development, executive breach communication |
| Offensive Security | Web app scanning, basic exploit usage | Active Directory attacks, privilege escalation chains | Red team operation planning, adversary simulation design |
| Cloud Security | IAM policy management, S3/Blob storage security | CSPM implementation, Kubernetes hardening | Multi-cloud security architecture, cloud-native SOC design |
| DevSecOps | Dependency scanning, secret detection in code | Threat modelling, SBOM generation and analysis | Product security program design, AppSec maturity models |
| GRC | Risk assessment basics, control gap identification | Risk quantification (FAIR), vendor risk management | Board-level risk reporting, M&A security due diligence |
| Detection Engineering | Sigma rule syntax, SIEM query basics | Detection coverage analysis, platform-specific rule conversion | Detection program strategy, threat-informed prioritisation |
| Threat Hunting | Hypothesis formulation, SIEM query proficiency | Statistical anomaly detection, hunt playbook development | Data science for security, hunt program metrics |
| Network Security | Firewall rule management, IDS/IPS tuning | Network segmentation, Zero Trust networking | Enterprise security architecture, SD-WAN security |
| AI Security | Prompt injection awareness, AI risk identification | AI red teaming, LLM guardrail implementation | AI security program development, EU AI Act compliance |
| Framework/Compliance | Framework navigation (NIST CSF, CIS), gap assessment | Multi-framework mapping, PCI-DSS/HIPAA implementation | Continuous compliance architecture, regulatory strategy |
| Security Behaviour | Phishing simulation management, metrics collection | Behaviour change methodology, insider threat indicators | Insider threat program management, behavioural science application |
| Tools | Command-line proficiency, packet capture analysis | Python security automation, SIEM administration | Custom tool development, security CI/CD pipelines |
| Career/General | Networking basics, home lab setup | Technical interviewing, security project portfolio | Budget management, executive communication |
The table above is a reference map, not a deep dive. For the full role descriptions, entry requirements, and salary ranges across all 15 domains, see the Cybersecurity Career Path: Complete Guide for 2026.
Top Cybersecurity Skills Employers Want in 2026
The ISC2 2025 hiring survey of 929 hiring managers across six countries identified the top technical skills employers want at entry and junior level: data security and encryption first, cloud security second, data analysis third, AI skills fourth, and risk assessment fifth (ISC2, 2025). Those survey results align closely with what the threat graph shows. The skills below are ordered to reflect both employer demand and current ransomware TTPs: the combination that tells you where the jobs are and why they exist.
Technical Cybersecurity Skills Employers Are Hiring For
Most skills lists are built from survey data alone. This one is cross-referenced against tracked ransomware family behaviour, which means the priorities below are grounded in what attackers do rather than what hiring managers say they want.
Cloud security is the #2 ranked technical skill in the ISC2 hiring survey and one of the three largest posting categories in CyberSeek's NICE Framework data (CyberSeek, June 2025). The majority of cloud breaches still come down to misconfigured permissions and over-privileged identities. IAM mismanagement is consistently the leading root cause, not sophisticated exploits. Skills that differentiate candidates: CSPM tooling (Prowler, ScoutSuite, Checkov), Kubernetes hardening, IAM least-privilege auditing, and IaC security scanning. Employers are increasingly specifying these individually in job postings rather than grouping them under a generic "cloud security" label.
Identity and access management sits behind the largest ransomware technique by family count. Valid Accounts (T1078) appears across 330 ransomware families and dozens of tracked threat actors, making credential abuse the most statistically dominant post-initial-access technique in the threat landscape. The two highest-ROI ATT&CK mitigations by technique coverage are User Account Management (M1018) and Privileged Account Management (M1026). MFA deployment, PAM implementation, and identity monitoring are the practical skills that implement them.
EDR deployment and ransomware response maps directly to the techniques used by virtually every active ransomware family. Data Encrypted for Impact (T1486) and Inhibit System Recovery (T1490) are each used by over 2,000 tracked ransomware families. Service Stop (T1489), used by 321 families to disable security tools before encryption, means defenders also need tamper-protection configuration and critical service monitoring. If you can configure EDR, validate backups, and execute a ransomware playbook, you're covering the techniques that matter most to the widest range of active threats.
Email security and phishing detection. Phishing (T1566) is used by more tracked threat actors than any other initial access technique, more than three times the next most common vector. Building SPF/DKIM/DMARC configurations, tuning email gateway sandboxes, and analysing spearphishing attachments are skills that directly address the most common way ransomware groups get in. The ISC2 hiring survey ranks data security (which includes email-layer controls) as the top technical skill overall.
PowerShell and command-line detection is where I'd push back on most career advice. The instinct is to learn to write PowerShell. The career value is in learning to detect it. Command and Scripting Interpreter (T1059) is used by 329 ransomware families across the CyberDesserts threat knowledge graph, and the Verizon 2025 DBIR confirms that System Intrusion is now the leading breach pattern by volume (Verizon, 2025). Script block logging, Constrained Language Mode, and AMSI integration are the specific controls. Understanding how malware abuses scripting interpreters, which I spent a lot of time on during frontline malware triage, gives you a very different mental model from someone who learned detection rules without that grounding.
Detection engineering is where threat data and career value intersect most sharply. The skill most career guides point to is writing Sigma rules. That is the starting point, not the finish line.
Sigma is a platform-agnostic detection format. Writing a rule in Sigma is the first step. The real work is converting it into the query language your SIEM understands: KQL for Microsoft Sentinel, SPL for Splunk, YARA-L for Chronicle. A rule that exists only in Sigma format does not run in any production environment. The practitioner who can take a detection, write it in Sigma, and deploy it as a working query in a live SIEM has done something a cert cannot replicate.
SMB/Windows Admin Shares abuse (T1021.002) is used by 45 ransomware families and dozens of threat actors. It has no public Sigma detection rules.
That gap is not a footnote. Practitioners who write detection for active techniques with real coverage gaps have outsized career value because the need is unmet and verifiable. For the full detection gap analysis, see the CyberDesserts Threat Landscape Report.
Supply chain security. APT41, one of the most technique-diverse tracked actors, uses supply chain compromise as a core TTP. SBOMs, dependency scanning, and third-party risk assessment are appearing in job postings on Indeed, LinkedIn, and ZipRecruiter as explicit requirements, not implied background knowledge.
Soft Skills Cybersecurity Hiring Managers Prioritise
The ISC2 2025 hiring survey ranked the top non-technical skills hiring managers want: problem-solving, analytical thinking, and critical thinking at the top, followed by teamwork, communication, and curiosity (ISC2, 2025). Communication has gained weight because AI adoption is increasing the need for practitioners who can explain security decisions to non-technical stakeholders and validate AI-generated outputs rather than accept them.
Threat modelling is partly a communication skill. Running a STRIDE session with a product team requires explaining attacker logic to engineers who don't think in attack trees. It's a skill built by doing it, not reading about it.
Emerging Cybersecurity Skills With the Biggest Talent Gap
AI security is the category with the sharpest talent shortage relative to demand. ISC2 ranks AI and ML as an area of critical skills deficiency and found that 72% of respondents expect AI to create demand for more strategic security mindsets across the field (ISC2, 2025). The ISC2 2025 hiring survey also places AI skills fourth in the ranked list of technical skills hiring managers want, ahead of risk assessment. The OWASP LLM Top 10 is the starting framework. Prompt injection testing and LLM guardrail implementation are the hands-on skills to develop.
SBOM literacy is emerging fast in regulated industries, particularly with EU AI Act enforcement beginning in August 2026 and ongoing SEC cyber disclosure requirements. Understanding CycloneDX format, SBOM generation, and using an SBOM for vulnerability triage is a genuine differentiator because most practitioners don't have it yet.
The Cybersecurity Career Playbook covers the broader skills that separate top performers at each stage, including several that don't appear in job postings until you're already in the room.
Best Cybersecurity Certifications by Career Level
Twenty years of watching hiring processes has taught me one thing about certifications: the ROI conversation almost never comes up, and it should. Cost, time commitment, and renewal overhead matter as much as the credential itself. Most advice on this topic ignores all three.
For a full certification roadmap mapped to career progression and domain specialisation, the Cybersecurity Skills Roadmap covers the sequencing in detail. The section below focuses on the highest-ROI choices at each stage.
Entry-Level Cybersecurity Certifications: Build the Foundation
CompTIA Security+ requires roughly 200 hours of study, costs $75/year to maintain via CE fees, and requires 50 CPEs every three years. It validates foundational security concepts across all five domains and is the most widely recognised entry cert for government and enterprise roles. Start here if you don't have one yet.
ISC2 CC (Certified in Cybersecurity) takes about 150 hours and costs $50/year in annual maintenance fees with only 15 CPEs required. It's lighter than Security+ in scope but covers the same conceptual ground and is free to sit for ISC2 members. It's the right choice if you want a credential while studying for Security+.
For DevSecOps specifically, the CSSLP (Certified Secure Software Lifecycle Professional) from ISC2 requires about 250 hours and costs $125/year in AMF fees. It validates secure software lifecycle knowledge and signals to employers that you understand security from the code perspective, not just the perimeter.
Mid-Level Cybersecurity Certifications: Prove Hands-On Competence
CompTIA CySA+ is 250 hours and $75/year. It covers threat detection and analysis mapped directly to the techniques most used by tracked threat actors. The CySA+ certification-to-threat mapping shows it prepares defenders for phishing analysis, PowerShell detection, and lateral movement monitoring across the most common attack techniques. Good ROI for blue team mid-career.
OSCP (Offensive Security Certified Professional) requires roughly 400 hours of hands-on lab work and has no renewal cost. It validates penetration testing proficiency through a 24-hour practical exam. At $1,749 for the course bundle, it's an investment, but employers trust it because it's not multiple choice. Skip it if you're staying purely on the defensive side. If you're doing any offensive or red team work, it's the credential that opens doors.
GWEB (GIAC Web Application Penetration Tester) takes about 300 hours and costs $479/year for renewal with 36 CPEs. It's the right mid-level cert for DevSecOps practitioners who need to validate web application security skills with a recognised GIAC credential.
Senior-Level Cybersecurity Certifications: Leadership and Architecture
CISSP requires approximately 400 hours of study, costs $125/year in AMF fees, and requires 40 CPEs annually. It validates security leadership and governance across eight domains. It's the standard credential for CISO track and senior leadership roles.
Here is the contrarian view most certification guides won't give you: a detection built in Sigma, converted into a working SIEM query, deployed against an active technique where detection coverage lags attacker activity, and documented on GitHub will do more for a mid-career candidate than a second cert. The ISC2 2025 Workforce Study is explicit that hiring organisations are prioritising demonstrated skills investment over credentials alone (ISC2, 2025). Hiring managers know the difference between someone who passed an exam and someone who built something that runs in production. Make sure your portfolio makes that distinction obvious before you spend another $1,500.
For senior DevSecOps practitioners, the honest answer is that no single cert defines the role at that level. SANS SEC540 provides the closest structured training for product security leadership, but the role is experience-driven. A strong portfolio of security programs you've built matters more than a cert at this stage.
If you want to hear it directly from the people making hiring decisions, What SOC Hiring Managers Test For is built around questions put to hiring managers across the industry. Their top five criteria for what separates standout candidates were all nontechnical. The cert question barely came up.
Cybersecurity Tools to Learn at Every Career Level
The threat graph provides a direct mapping from attacker tooling to defender priorities. Cobalt Strike appears in 28 ransomware group operations and across 72 tracked malware techniques in the knowledge graph. Mimikatz appears in 25 ransomware group operations. These are not academic references. They are the tools defenders encounter in live incidents.
Understanding attacker tooling is how you train your detection rules on what they should be catching.
Entry-Level Cybersecurity Tools to Learn First
Wireshark and tcpdump for packet capture and protocol analysis. Every security role at some point requires reading traffic.
Nmap and Nessus/OpenVAS for network enumeration and vulnerability scanning. Understanding what's on the network is the starting point for both offence and defence.
SonarQube and Snyk for DevSecOps entry: these two tools appear in most CI/CD security pipelines. Knowing how to configure them and triage their output is table stakes for AppSec roles.
Sysmon and Splunk (free tier) for detection: Sysmon is free, covers critical Windows event collection, and feeds every SIEM. Building Splunk searches on Sysmon data is the fastest way to develop detection skills in a home lab.
Mid-Level Cybersecurity Tools That Differentiate You
Sigma CLI and Uncoder.io for detection engineering. Sigma is the platform-agnostic layer. Uncoder.io converts it into the query language your SIEM runs: KQL for Sentinel, SPL for Splunk, YARA-L for Chronicle. The combination of writing a rule and deploying it as a working query in a live platform is what detection engineering roles will test. If you can also target techniques where detection coverage lags attacker activity, better still.
BloodHound and Impacket for Active Directory attack understanding. Defenders who understand BloodHound attack paths know exactly where to break the kill chain. When I was doing malware triage, the tools that made me effective were the ones designed to surface attacker behaviour, not just detect it. BloodHound works the same way from the other side.
Semgrep for mid-level DevSecOps: moves beyond basic dependency scanning into custom rule writing and code pattern analysis. The open-source version is free, extensible, and what most practitioners learn independently before encountering enterprise alternatives.
Velociraptor for incident response. It's the enterprise endpoint visibility tool that DFIR practitioners rely on for large-scale hunt and collect operations.
Senior-Level Cybersecurity Tools: What You Build With
Detection-as-Code pipelines using GitHub Actions or GitLab CI: at the senior level, detection rules are treated like software, with version control, testing, and deployment automation.
SBOM generators (CycloneDX) for product security: generating and managing SBOMs at scale is a senior DevSecOps function that's becoming a regulatory requirement in many industries.
Custom Python tooling connects most senior security functions: from SOAR playbook automation to custom log parsers to threat intel enrichment pipelines. Senior practitioners who can't script are limited in how far they can scale their programs.
For web security hands-on practice at any level, CookieJar Lab covers session hijacking, cookie security, and infostealer simulation in a test environment.
Security Trends Shaping Cybersecurity Careers in 2026
Four trends are directly reshaping what employers hire for and what practitioners need to develop. Each one has a clear skills implication. The sections below cover what that looks like in practice.
AI Security Jobs in 2026: Skills, Demand, and Where to Start
AI adoption is creating security roles that didn't exist three years ago. The NCSC assessment of AI's impact on the cyber threat confirms that generative AI is making phishing harder to detect and accelerating vulnerability exploitation and social engineering attacks (NCSC, 2025). Defenders need to understand both the new attack surface and the defensive tools.
The OWASP LLM Top 10 covers prompt injection, insecure output handling, training data poisoning, and model denial of service. Practitioners who can test LLM applications against this framework are ahead of the majority of the field. The MITRE ATLAS framework maps adversarial ML techniques the same way ATT&CK maps traditional threats: start there for structured learning.
AI is also changing how detection teams work. High-volume alert triage, log analysis, and SIEM monitoring are the tasks most affected by AI tooling, which means practitioners need to shift toward higher-judgment work: building detection logic, validating AI outputs, and responding to incidents that automated systems can't handle alone.
Cloud Security: The Fastest-Growing Cybersecurity Domain
Cloud security roles now span three distinct areas: cloud-native security for workloads (CSPM, container security), cloud identity and access management, and cloud forensics for IR. Job postings increasingly require specific platform certifications (AWS Security Specialty, AZ-500) alongside generic security credentials.
Kubernetes hardening has gone from niche to standard. Most enterprises running microservices architectures have Kubernetes clusters that need security configuration review, network policy management, and runtime threat detection. If you're building cloud security skills, put Kubernetes on that list.
Supply Chain Security: From SolarWinds to Standard Practice
APT41, one of the most technique-diverse tracked actors, uses compromise of software supply chains as a core technique. Supply chain attacks moved from advanced threat territory to common enough that CIS Control 15 (Service Provider Management) and Control 2 (Software Asset Inventory) are now baseline requirements, not aspirational targets.
SBOM tooling is the practical skill here. CycloneDX is the dominant open standard. Dependency scanning, SBOM generation, and third-party risk assessment are the skills that translate to job titles like Application Security Engineer and Supply Chain Risk Analyst.
Detection Engineering: The Highest-Demand Blue Team Cybersecurity Role
Detection engineering portfolio questions come up repeatedly across the community: how to get started, what to build, and how to make it stand out to hiring managers. That's consistent with the broader market signal: detection engineering is the blue team specialisation with the sharpest skill shortage. The February 2026 Career Report covered detection engineering as a top technical skill, and the demand signal has only strengthened since.
The detection gap data makes the career case: SMB/Windows Admin Shares abuse (T1021.002) is used by 45 ransomware families and dozens of tracked threat actors but has no public Sigma detection rules. The full skill is writing the rule in Sigma and converting it into a working query in your SIEM: KQL, SPL, or YARA-L depending on the platform. Practitioners who do that for active techniques with coverage gaps are filling a real need, not padding a resume. The SANS SEC555 course is the structured path, but the Sigma HQ documentation, Uncoder.io, and Atomic Red Team labs can get you started for free.
Zero Trust: Identity-Centric Cybersecurity Architecture
Valid Accounts (T1078) appears across 330 ransomware families and 56 tracked threat actors. The mitigation is well-understood: MFA, PAM, and identity monitoring. Zero Trust implementation is the framework that operationalises these mitigations at scale.
Practitioners who understand Zero Trust networking, not just the marketing concept but network segmentation, microsegmentation, and identity-aware proxies, have skills applicable across enterprise, cloud, and hybrid environments. The book Zero Trust Networks by Evan Gilman and Doug Barth is the practitioner's read, not the vendor's white paper.
Breaking Into Cybersecurity: Career Switcher Advice for 2026
The opportunity is real. CyberSeek's June 2025 data recorded nearly 500,000 U.S. cybersecurity job postings, and 59% of hiring teams report critical skills gaps they cannot fill (ISC2, 2025). The entry point is achievable. But the path matters.
First steps that work. Get Security+ (roughly 200 hours, $75/year to maintain) and build a home lab simultaneously. The cert without the lab tells a story on paper. The lab without the cert doesn't pass resume filters. You need both. TryHackMe's Pre-Security path and SOC Level 1 path are free-to-low-cost and structured enough to follow without a mentor. A full curated list of free and low-cost resources by career path is in Free Cybersecurity Training: Resources by Career Path.
For DevSecOps specifically. If you're coming from software development, you have a head start most career switchers don't: you understand CI/CD pipelines, Git, and how code ships. Add OWASP WebGoat and PortSwigger Web Security Academy to your practice stack and start working through the OWASP Top 10 in code, not just in slides. GitGuardian's free tier lets you scan your own repos for secrets, which is also how you understand what the tools are detecting.
For the reading path that maps to a technical background entering DevSecOps, Best Cybersecurity Books 2026 covers the reading specifically mapped to DevSecOps and career changers from technical backgrounds.
Common mistakes. Chasing certs without building a portfolio. The ISC2 2025 Workforce Study is clear that skills investment, not headcount, is what hiring organisations are prioritising, and hiring managers expect candidates to demonstrate that investment with evidence they can walk through, not credentials alone (ISC2, 2025). A GitHub repo with a home lab write-up and a detection deployed as a working SIEM query beats a second cert every time.
Skipping networking fundamentals. TCP/IP, DNS, and how traffic flows are prerequisites for most detection and analysis work. If you don't have a networking background, David Bombal's YouTube content covers the fundamentals well before you spend money on a course.
Resources worth your time.
The DevSecOps Playbook by Sean D. Mack gives you the mental model for how security integrates into software delivery. Read it before your first DevSecOps job, not after.
Threat Modeling: Designing for Security by Adam Shostack is the practitioner's guide to STRIDE and systematic threat analysis. It teaches the methodology, not just the output.
The OWASP community and r/devsecops are where working practitioners discuss real problems. The signal-to-noise ratio is better than most forums. For book recommendations across all 15 security domains ranked by career stage, see Best Cybersecurity Books 2026.
For hands-on web security practice, CookieJar Lab covers session hijacking, cookie attacks, and infostealer simulation in a safe environment. It's a concrete starting point for building web security skills beyond theory.
If you're coming from a degree programme rather than an IT background, the Cybersecurity Graduate Guide maps the gap between academic knowledge and job-ready skills more precisely.
What the April 2026 Cybersecurity Job Market Tells You
The skills gap is measurable: 59% of security teams report critical or significant deficiencies, and the most recent U.S. job postings data shows nearly 500,000 open positions (ISC2, 2025; CyberSeek, June 2025). DevSecOps sits at the convergence of the fastest-growing technical demands: supply chain security, cloud-native security, and shifting security left in software delivery.
The threat landscape is not abstract career advice. The techniques attackers use most (phishing, PowerShell execution, credential abuse) translate directly into the defensive skills employers hire for. Build detection for real gaps, get hands-on with the tools ransomware operators use, and match your certifications to your career stage.
And before you spend money on another cert, ask whether a detection built in Sigma, converted into a working SIEM query, and deployed against an active technique where detection coverage lags attacker activity would do more for your career. The data suggests it would.
For personalised guidance on which path fits your background, the CyberDesserts Learning Assistant provides tailored career advice based on your current experience and goals.
Map your full progression with the Cybersecurity Skills Roadmap, and build hands-on web security skills with CookieJar Lab.
The gap between knowing and doing is where most careers stall. The practitioners who move fastest are not the ones with the longest certification list. They are the ones who built something before they felt ready and showed their work before they thought they had enough to show.
Start there.
Frequently Asked Questions About Cybersecurity Careers
Do I need a degree to get into cybersecurity? No, but you need a portfolio. Certifications like Security+ clear resume filters, and documented home lab projects demonstrate hands-on competence. Many employers, per CyberSeek data, list certifications and skills as primary requirements, with degrees listed as preferred rather than required.
Which certification should I get first? Security+ if you have no prior credentials. ISC2 CC if you want something to show while you study for Security+. Both are the answer if you're targeting government or enterprise roles. For DevSecOps specifically, add CSSLP after Security+ rather than jumping to CISSP.
How long does it take to get hired in cybersecurity? Most career switchers with a focused study plan, a home lab, and a Security+ cert are competitive for entry roles within six to twelve months. The range varies by prior IT background. Coming from software development into DevSecOps often takes less time because of transferable skills.
What certifications do SOC analysts need? CySA+ (250 hours, $75/year) is the most relevant entry-to-mid cert for SOC roles. The Splunk Core Certified User cert is free to renew and validates the SIEM skills every SOC analyst uses daily. Add GCIA for mid-career if you want to specialise in network intrusion analysis.
What skills are most in-demand for threat intelligence analysts? The top skills from the data: OSINT research, IOC analysis, MITRE ATT&CK framework navigation, and YARA rule writing. YARA rule writing is the mid-level skill with the clearest career value signal: it maps directly to detection needs driven by real threat actor activity.
Should I specialise in offensive or defensive security? Decide based on what kind of work energises you day to day, not on salary projections. Both paths pay well at mid-to-senior level. Offensive roles (pen testing, red team) require sustained practice and a strong lab portfolio. Defensive roles (SOC, detection engineering, IR) have more entry-level openings and a clearer progression path.
How do I build a detection engineering portfolio? Start with the Sigma HQ documentation and write rules for common techniques: PowerShell execution, scheduled tasks, registry persistence. Then convert each one into a working query for a SIEM platform: KQL if you are targeting Sentinel, SPL for Splunk, YARA-L for Chronicle. Use Uncoder.io to handle the conversion and validate the output logic. Run the technique with Atomic Red Team in a lab, confirm the query fires, document the full process on GitHub, and publish a write-up. That is a portfolio entry. Not the Sigma rule alone, but the complete pipeline from detection logic to deployed query. Repeat with techniques where detection coverage lags attacker activity, such as SMB admin share monitoring, and you are demonstrably ahead of most applicants.
References and Sources
- CyberSeek. (June 2025). CyberSeek Cybersecurity Workforce Data. Key finding: 514,000 U.S. cybersecurity job postings; estimated global cybersecurity workforce of 4.97 million (range: 4.4M to 5.5M).
- ISC2. (2025). 2025 ISC2 Cybersecurity Workforce Study. Data collected May/June 2025; 16,029 respondents. Key findings: 95% report at least one skills deficiency (up 5% from 2024); 59% cite critical or significant skills gaps (up 15% from 2024); ISC2 did not publish a headline workforce gap estimate in 2025, noting that skills shortages are a more pressing measure than headcount; AI ranked as a critical skills deficiency area; 72% of respondents expect AI to require more strategic security mindsets; organisations are investing in upskilling existing staff over headcount growth.
- ISC2. (September 2025). 2025 Cybersecurity Hiring Trends: Skills Deep Dive. Survey of 929 hiring managers across six countries. Key finding: top technical skills at entry and junior level are data security, cloud security, data analysis, AI skills, and risk assessment, in that order. Top personality attributes: problem-solving, analytical thinking, critical thinking.
- Verizon. (2025). 2025 Data Breach Investigations Report (DBIR). Analysis of 22,052 security incidents and 12,195 confirmed breaches across 139 countries. Key finding: System Intrusion, involving scripting, malware, and ransomware, is now the leading breach pattern by volume; ransomware present in 44% of all confirmed breaches; credential abuse the leading initial access vector.
- NCSC. (2025). The near-term impact of AI on the cyber threat. Key finding: Generative AI is increasing the difficulty of identifying phishing, accelerating vulnerability exploitation, and amplifying social engineering at scale.
- MITRE Corporation. (2025). MITRE ATT&CK Framework. Key finding: Phishing (T1566) is the most widely documented initial access technique across tracked threat actors.
- OWASP. (2025). OWASP LLM Top 10. Key finding: Prompt injection, training data poisoning, and insecure output handling are primary risks in LLM deployments.
- CyberDesserts. CyberDesserts Threat Intelligence Knowledge Graph (cumulative, queried April 2026). Key findings: SMB/Windows Admin Shares (T1021.002) used by 45 ransomware families with no public Sigma detection coverage; Command and Scripting Interpreter (T1059) used by 329 ransomware families; Valid Accounts (T1078) used by 330 ransomware families. Technique counts are cumulative across all tracked actors and families in the knowledge graph.
- The DFIR Report. (2025-2026). Real-world intrusion case studies. Key finding: Cobalt Strike, Mimikatz, PsExec, and AnyDesk are the most frequently observed tools in tracked ransomware operations.
About This Report
Report month: April 2026. Spotlight domain: DevSecOps.
Most cybersecurity career reports are built on survey data alone. This one adds a layer most career content does not have: the CyberDesserts threat intelligence knowledge graph, a curated dataset covering thousands of tracked threat actors, ransomware families, ATT&CK techniques, and public detection rule coverage. The editorial link is direct. The techniques attackers use most frequently are the skills defenders need most urgently. The gaps in public detection coverage are where skilled practitioners are scarcest and most valuable.
Technique rankings are cumulative counts across the full knowledge graph, not filtered to 2026 activity. They represent historical accumulation across all tracked campaigns, which is the right framing for career planning. The techniques used across hundreds of actor profiles and thousands of ransomware families are the ones defenders need to understand regardless of when any individual campaign ran. Where recency matters, such as ransomware group activity status, the data uses a 90-day active window. Workforce data is from the ISC2 2025 Workforce Study and CyberSeek June 2025 snapshot, the most recent primary publications available.
Skills demand is derived from attacker behaviour, not certification vendor marketing. The knowledge graph cross-references technique prevalence against public detection rule coverage to identify where attacker activity outpaces defensive tooling. Those gaps are where skilled practitioners are most scarce and where a documented, deployed detection carries real career weight. Workforce claims are sourced from named primary studies. Certification data covering study hours, renewal costs, and CPE requirements is sourced from structured records.


Member discussion