Linux Basics for Hackers: Essential Commands for Cybersecurity Professionals
Article Content
Over 96% of the world's top 1 million web servers run on Linux (W3Techs). Meanwhile, 100%
A Guide to Cybersecurity Maturity Models
Learn how to benchmark your security program understand cybersecurity maturity levels within NIST, CMMC, and HMM, for a strategic roadmap.
Four Threat Shifts That Will Define the 2026 Security Landscape
How the threat landscape shifted in 2025 and what to expect in 2026
Splunk Enterprise Docker Setup: Quick Start Guide for Security Testing
Build a Splunk Enterprise security monitoring environment with Docker in 30 minutes. Learn to deploy Splunk in a container, configure
Gartner's 2025 Supply Chain Prediction: A Retrospective Look at What Actually Happened
LinkedIn
Post
Copy Link
In 2021, Gartner made a bold prediction: by 2025, 45% of organizations worldwide would experience attacks
AI Browser Security Risks: What to Know
Updated April 2026
This article covers browser-specific risks. For the broader agentic AI security picture including MCP security, OpenClaw, and
Cloud Security Fundamentals: What Every Organization Needs to Know
Ninety-four percent of enterprises now use cloud services, yet cloud misconfigurations remain the leading cause of data breaches. If your
Cybersecurity Career Playbook - 2026
18 CYBERSECURITY SKILLS THAT SEPARATE TOP PERFORMERS
AI and Cybersecurity: Some Interesting Thoughts from a Recent Podcast Chat
TL;DR: Attackers build unrestricted AI models while defenders work within ethical guardrails, creating a dangerous asymmetry. Your expertise determines how much AI amplifies your productivity. And sometimes the most sophisticated AI systems still fail because of a default password.
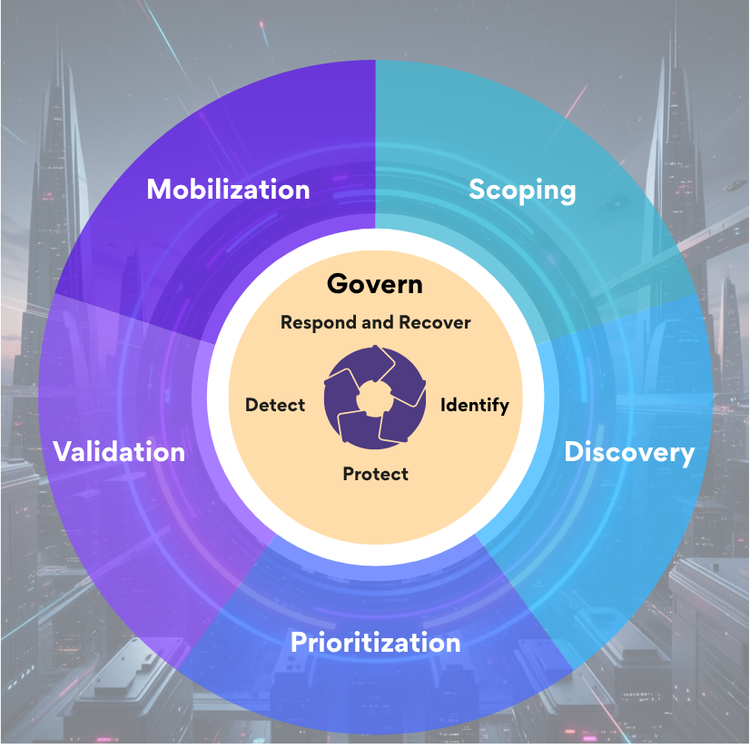
Why NIST Aligned CTEM Is the Framework Integration Security Teams Need
TL;DR - Discover how NIST aligned CTEM transforms framework compliance into operational security. Bridge governance maturity and real threat detection through continuous validation of NIST CSF 2.0 controls.